The U.S. government is pushing companies to tighten security around Microsoft endpoint management tools after a cyberattack disrupted Stryker Corp operations.
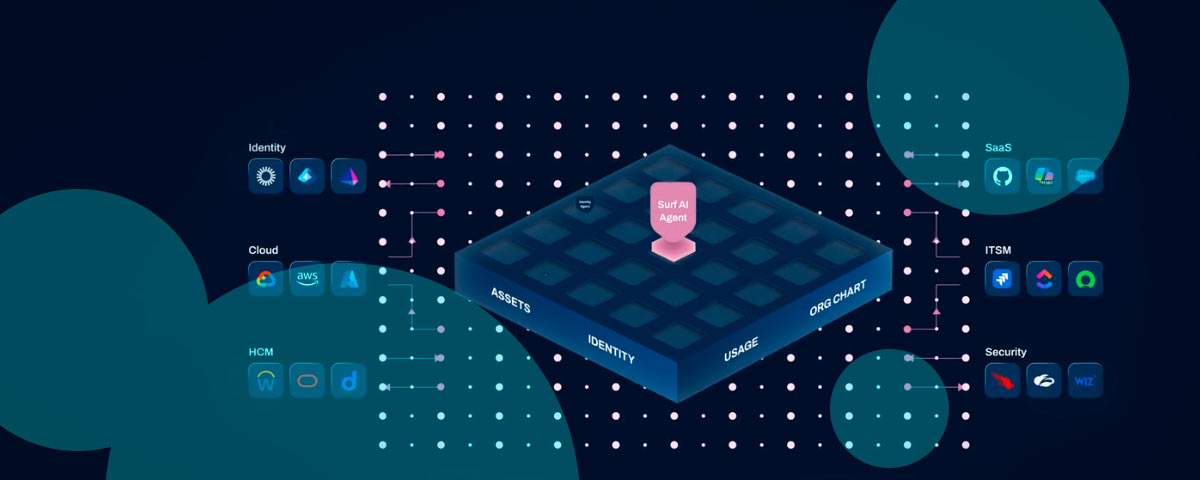
The incident exposed weaknesses in how organizations manage access, devices, and applications across enterprise systems.
On March 11, 2026, medical technology giant Stryker suffered a significant cyberattack, suspected to be carried out by the pro-Iran group Handala, which disrupted global operations by wiping data on thousands of employee devices.
The company reported issues processing orders, manufacturing products, and shipping to customers. Operations slowed across multiple regions. Recovery took time, even after containment.
The attackers bypassed traditional malware, using legitimate administrative tools to target Stryker’s Microsoft-centric environment, causing widespread disruptions in manufacturing, shipping, and order processing.
According to Stryker, “all products across global portfolio, including connected, digital, and life-saving technologies, remain safe to use. This event was contained to Stryker’s internal Microsoft environment, and as a result it did not affect any of our products – connected or otherwise”.
“Stryker, much like any Fortune 300 company, has embedded policies and procedures for cybersecurity assurances for our products in the field. This process at Stryker provides additional assurances that no potential vulnerabilities or risk of exploitation related to our connected products exist”.
Per standard protocols, Stryker have leveraged this process to confirm that connected products were not impacted by the incident and remain safe to use
An Iran-linked group known as Handala claimed responsibility for the attack. The group framed the incident as retaliation tied to geopolitical tensions.
The attack underscores the increasing vulnerability of major medical manufacturing supply chains to sophisticated cyber threats that target third-party infrastructure.
Attribution remains under review, though the claim adds another layer of risk for multinational firms.
The Cybersecurity and Infrastructure Security Agency issued a direct warning following the breach. Officials said they are tracking malicious activity targeting endpoint management systems across U.S. organizations.
The Stryker case appears part of a broader pattern, not an isolated event.
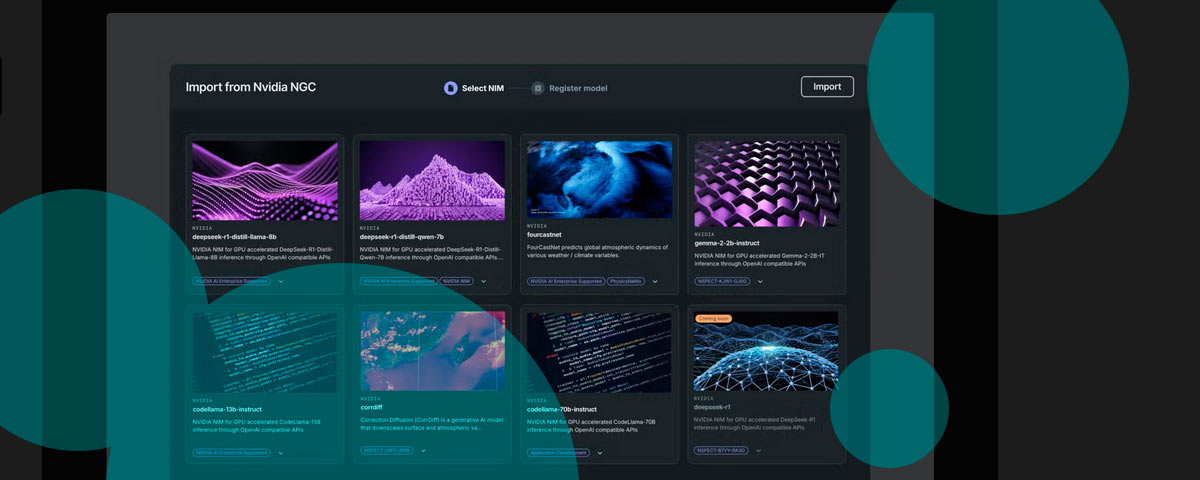
CISA urged companies to strengthen system configurations immediately. The agency pointed to Microsoft Intune, widely used to manage devices and user access.
Key Details of the Stryker Attack
- The attackers, believed to be the Iran-linked Handala group, claimed to have wiped hundreds of thousands of systems, though reports suggest around 80,000 devices were impacted.
- The incident was a “wiper” attack, exploiting legitimate administrative tools (likely Microsoft Intune) rather than deploying traditional malware, allowing the hackers to wipe machines and data.
- The breach hit corporate IT and logistical systems, causing disruptions to the manufacturing, shipping, and scheduling of critical hospital supplies.
- Stryker stated the attack was contained, no ransomware was used, and that its external, connected medical devices were not impacted.
- The attack is considered a significant instance of Middle East conflict spilling over into U.S. infrastructure, with claims it was in retaliation for military actions in Iran
Organizations should follow Microsoft’s security guidance, tightening controls and reducing exposure across endpoints.
Federal agencies are coordinating response efforts. CISA is working alongside the Federal Bureau of Investigation to assess threats and define mitigation steps.
The focus stays on preventing lateral movement across networks once attackers gain entry.
Operational disruption extended beyond internal systems. Reports indicate the attack delayed certain surgical procedures. That impact underscores how cyber incidents now affect physical services, not only digital infrastructure.
Stryker said it contained the attack and restored affected systems. The company stated patient-related services and connected medical devices were not compromised.
It has not disclosed financial impact tied to the disruption.
According to Beinsure analysts, endpoint management systems present high-value targets because they control access across entire organizations.
A single compromise can cascade quickly through networks, especially when security controls lag behind system complexity.