Overview
In a highly digitised economy, cybersecurity and cyberinsurance sits at the top of the agenda for businesses, boards, risk managers and governments alike.
In recent years, malware and ransomware cyberattacks have been causing severe disruption for global businesses and their supply chains. In addition to the rise in malware and ransomware attacks, the threat of state-sponsored cyber-attacks has become a significant focus for businesses and governments.
Shifting powers: Physical cyber risk in a changing geopolitical landscape Lloyd`s Report focuses on the importance of effective risk management and the role of insurers in helping customers build resilience to cyber-attacks that could cause damage to physical environments.
Produced in partnership with the Cambridge Centre for Risk Studies, the report uses scenario-based analysis to help manage uncertainty around the interconnected threat of cyber and geopolitics, looking specifically at the perils of state-sponsored cyber-attacks.
Lloyd’s understand the complex and potentially systemic risks in the cyber class and are committed to supporting a resilient cyber market.
Cyber physical represents a key opportunity for insurers to develop a sustainable cyber risk offering that can help protect customers from a risk that has reached the highest level of priority in boardrooms around the world.
Whilst most cyber-attacks are digital, some result in tangible disruption or damage to the physical environment – these types of attacks are becoming increasingly common place. This is, in large part due to the increasingly interconnected nature of systems and services which expose businesses to perils from physical cyber-attacks such as fires, explosions, flooding or bodily injury.
Those trends have been underlined by the COVID-19 pandemic and the rise in criminal ransomware activity it triggered; alongside the changing geopolitical landscape in the wake of Russia’s invasion of Ukraine. Thankfully, the world is yet to experience a truly catastrophic cyber physical attack. But the potential impacts of such an attack could be significant, crippling entire systems and societies.
For the most part, cyber attacks target the availability, confidentiality or integrity of data – rather than causing operational, environmental or material damage. In some cases, however, the disruption that follows cyber attacks can have a destructive impact on the physical world. This is a growing threat, with attacks targeting critical infrastructure rising from less than 10 in 2013 to almost 400 in 2020. As well as the increase in frequency, the complexity of attacks are evolving, from simply targeting short-term disruption to compromising assets or processes with the intent to cause physical harm or loss of life.
In this context: an effective cybersecurity strategy is paramount. With a risk as complex as cyber insurance – encompassing a huge range of possibilities and uncertainties – one useful tool for risk managers can be scenario planning.
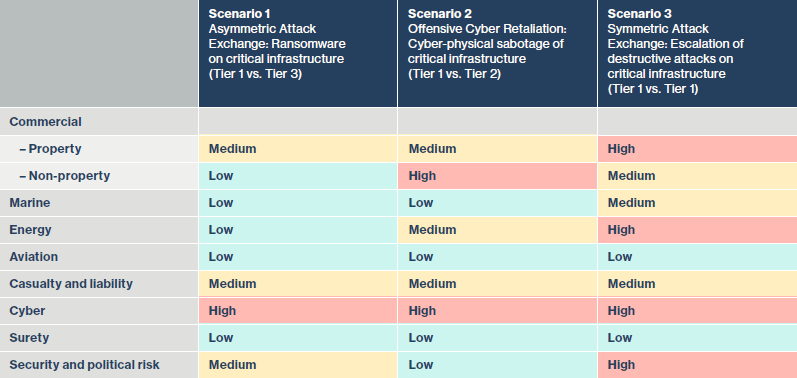
This report outlines three hypothetical, but plausible scenarios involving politically motivated cyber attacks intended to cause physical damage. The analysis includes the potential impacts on businesses and the insurance industry.
While geopolitical interests to date have broadly deterred actors from using their advanced cyber security and capabilities – as the scenarios developed in this report demonstrate, circumstances can quickly escalate; and the anonymous nature of cyber attacks could allow states and other geopolitical players to deploy espionage, retribution, and attacks with broad plausible deniability. Placed in a climate of increased tension, the risk of a major cyber attack affecting physical systems, national infrastructure and the global economy becomes far more likely.
Physical cyber risk
In recent years, the worlds of cyber and geopolitics have become increasingly integrated. Concern over the digital interference of state actors with foreign elections has been a visible issue since at least 2015; however digital intrusion, and the projection of unseen influence by state-backed cyber teams, has been around since the turn of the millennium.
Historically, cyberspace has been the domain of non-state actors.
Cyber criminals, hacktivists, and other entities have successfully mapped closed networks and exploited secure systems, creating a dark economy of toolkits, services-for-hire, and intelligence that are easy to purchase and develop over time.
As a result, the stealing of data, funds, and intelligence in order to project substantial power online is more accessible than ever – to a broader swathe of actors. This includes nation states, non-state threats, insurgents and other unpredictable, maliciously minded groups.
For the most part, state-sponsored cyber operations have been used to gather intelligence and influence real- world politics. However, cyber space offers an opportunity for smaller states to project power beyond traditional military or economic arenas. In these countries, cyber actors are rapidly raising profile. There are also clear signs that a number of states have assembled powerful cyber arsenals, with tools capable of crippling major industries or state projects through economic and physical disruption. Barring a few notable examples, most nations are not known to have carried out attacks using these tools. However, state-sponsored cyber activity is arguably more prevalent – albeit slower moving, largely covert and deployed alongside other foreign policy tools such as sanctions.
Put simply, we don’t yet see the damage brought about by sophisticated state- backed cyber attacks – although that doesn’t mean they’re not happening. As cyber risk and geopolitics have become more closely integrated, cyber attacks affecting physical systems and structures can be both a cause and effect of the changing geopolitical landscape. They may therefore become more obvious and impactful as the geopolitical landscape changes.
Cyber physical scenarios
Developing hypothetical scenarios can be a useful tool for managing uncertainty, especially for risks that are not well understood.
They can help with contingency plan development or the testing of mitigation strategies, for example through wargaming exercises or workshops among senior staff. This understanding can be applied to help with decision making about the future, and facilitate the reporting, management, and mitigation of risks.
The scenarios described here demonstrate plausible circumstances in which deterrents may fail, leading to an escalation of the threat landscape. The circumstances described in each scenario involve major cyber actors but also consider the roles that smaller, developing states or other groups such as activists or terrorists may play in contributing to physical cyber disruption.
For the purposes of these scenarios, the countries are given the names of planets in the solar system:
- Scenario 1 – Asymmetric Attack Exchange: Ransomware on critical infrastructure
- Scenario 2 – Offensive Cyber Retaliation: Cyber-physical sabotage of critical infrastructure
- Scenario 3 – Symmetric Attack Exchange: Escalation of destructive attacks on critical infrastructure
Adopting the International Institute for Strategic Studies (IISS) new methodology for assessing cyber power, we identify three broad categories or ‘tiers’ of cyber operations through which to discuss geopolitical tensions and escalations.
For the purposes of these scenarios, the countries are given the names of planets in the solar system. Adopting the International Institute for Strategic Studies (IISS) new methodology for assessing cyber power, we identify three broad categories or ‘tiers’ of cyber operations through which to discuss geopolitical tensions and escalations.7
Countries in these tiers are assessed across in seven categories of cyber capability:
- Strategy and doctrine,
- Governance, command and control,
- Core cyber-intelligence capability,
- Cyber empowerment and dependence,
- Cyber security and resilience,
- Global leadership in cyberspace affairs,
- Offensive cyber capability.
Tiers allow for the anonymous discussion of the impacts of nations or other groups engaging in cyber conflict and other geopolitical statecraft.
Scenario 1 – Asymmetric Attack Exchange: Ransomware on critical infrastructure
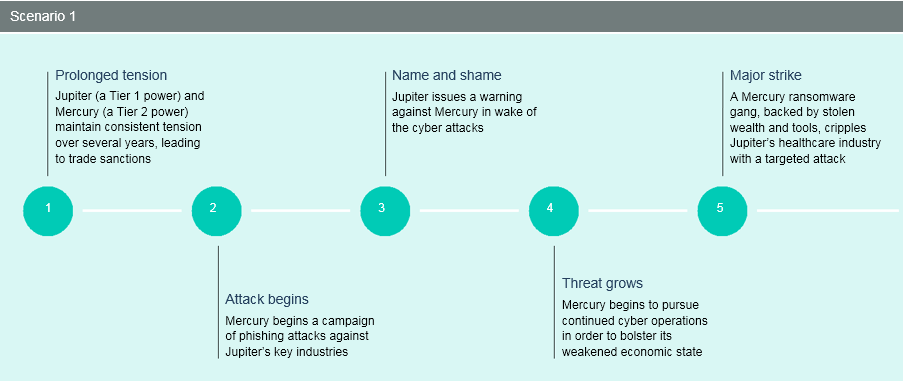
On the back of increasing geopolitical tensions between Jupiter and its regional rival Mercury, the former introduces a series of sanctions against the latter, significantly harming its ability to channel funds for various state-run projects. Shortly after, Jupiter’s intelligence agency begins to notice an increase in phishing attacks originating from Mercury and targeting organisations within its borders and in the broader region.
Scenario 2 – Offensive Cyber Retaliation: Cyber-physical sabotage of critical infrastructure
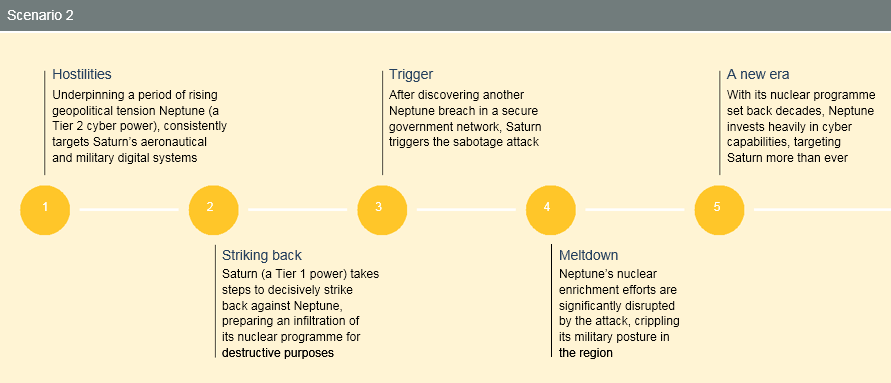
Following years of escalating geopolitical tensions with Neptune, and countless cyber espionage attacks, Saturn goes on the offensive and puts into practice a shift in its national cyber security strategy, which allows the use of offensive cyber operations in response to security challenges and concerns in the cyber space.
Scenario 3 – Symmetric Attack Exchange: Escalation of destructive attacks on critical infrastructure
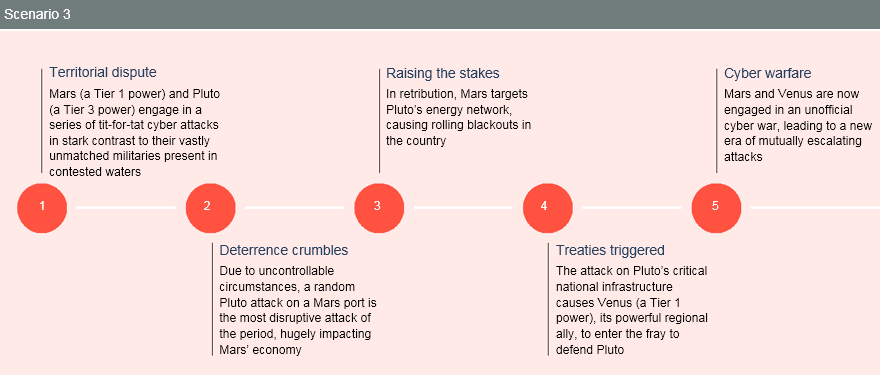
As geopolitical tensions escalate in contested waters amid competing exclusive economic zone claims between regional rivals, state-sponsor cyber groups backed by emerging regional and global power Mars carry out a series of fleeting but disruptive attacks against the telecommunications infrastructure of aspirational regional middle power Pluto – against which it holds maritime and territorial claims. The attacks, range from disguised ransomware operations, to distributed denial-of-service (DDoS) attacks, to data thefts and leakages, all forcing affected companies to temporarily suspend operations and shut down critical services that consumers and businesses rely on, causing far-reaching disruption.
Once they have established the origin of the attacks, Pluto’s modest but rapidly developing cyber collective counters by launching sustained DDoS attacks on a Mars port-management network. Flooding and overwhelming one of the country’s busiest shipping terminal port’s networks with fake traffic from multiple sources, the attack overloads operational technology (OT) systems and prevents operations from being safely fulfilled. This keeps cargo movement on hold for hours and significantly disrupts operations.
Understanding cyber physical risk
Most cyber attacks on networks are disruptive in nature, affecting the availability, confidentiality or integrity of data, rather than operational safety, environmental safety, or human lives. Put simply, most cyber attacks inflict damage chiefly by shutting down regular business activity. The massive losses seen in the 2017 NotPetya attack, for instance, came from disrupted business, lost sales, reputational damage, and in the repair and replacement of key technology.
In some cases, however, cyber attacks that focus on data can also have a destructive impact on the physical world.
A ransomware attack on a hospital’s network, for example, may threaten the lives of patients by interrupting the data flow to critical medical tools. This concern has grown throughout the pandemic, even though some ransomware gangs originally issued statements to say that they would not target healthcare networks during the covid outbreak. In 2020, the first death attributed to a ransomware attack was reported in Germany.
Cyber physical attacks trigger physical damage or injury purely by compromising operational technology (OT) and digital control systems or disabling control and safety systems. This includes attacks on Supervisory Control and Data Acquisition (SCADA) systems. Some cyber physical attacks may be targeted (focused on bringing down a particular piece of technology, such as a furnace or fuselage) while others may impact multiple devices across networks, such as batteries or boilers. There is generally a smaller pool of OT or SCADA service providers, compared to enterprise IT for example, which increases the potential risk for businesses.
Cyber deterrence
In a highly digitised economy, fear of escalating cyber conflict has become a constant for businesses and governments alike (effective ways mitigate cyber risk). For much of the past decade, a deterrence- based geopolitical climate has largely prevented any public, openly aggressive cyber engagement by states.
US Cyber Strategy explicitly stated an intention to “defend forward” against cyber adversaries – perhaps heralding a transition from the age of deterrence to one where defence and offence are harder to separate.
These new postures directly acknowledge the present threat to vital systems and critical national infrastructure from rival nations and geopolitical entities. At present, however, deterrence appears to be a powerful force in warding off such action. Deliberate ‘cyber catastrophes’, as a result of cyber operations by major powers, remain unlikely.
At present, states are at a point of equilibrium; powerful cyber teams have proved either unwilling or incapable of causing catastrophic economic impact, yet could plausibly advance the threat suddenly and significantly. However to date, national cyber policies have not differed substantially from foreign policy instruments – including the use of miilitary force and coercive diplomacy. So while cyber is a powerful tool, it is unlikely to be used in a destructive way independent of significant shifts in a nation’s foreign policy, as any escalation would quickly prove disastrous.
The involvement of non-state actors, however, increases the risk of cyber catastrophes. As these, often extremist, groups gain traction in cyber operations – intending to cause major shocks to national or international systems, and often with little to lose strategically – the risk of cyber terrorism, cyber protest, and other forms of cyber insurgency increases. Questions remain around precisely how cyber operations can deliver the seismic change many of these groups seek: for example, some radical environmental groups may target the destruction of a major pipeline, but achieving this through cyber means is difficult, expensive, and time-consuming. This means more reliable physical attacks and protests are likely to be relied upon for the foreseeable future.
The threat to businesses
Despite the political sponsors who sit behind this threat, the nature of cyber disruption means that it is largely immune to geographical boundaries. Any major change in the cyber threat landscape which increases the sophistication of tools in wide circulation, or lowers the bar for achieving highly impactful attacks, will increase risk to businesses across multiple geographies. Attacks may become more frequent, or more severe in nature, and businesses may be strategically disrupted in order to deal blows to national interests, or suffer from the knock-on consequences of a major cyber attack to critical national infrastructure.
Businesses are also vulnerable to attacks which affect third-party suppliers with less secure networks, or which are located in parts of the world where cyber disruption may increase sharply and suddenly. This has the potential to be disastrous for businesses who are reliant upon them for their supply chains, especially multinational firms with digital supply chains which stretch across multiple complex networks.
What cyber physical attacks can and can’t do
Industrial and highly mechanised environments, including national infrastructure systems, building control managers, energy management systems, traffic grids, and other utilities which aid in business continuity and national safety are all highly vulnerable to cyber attack.
Cyber crime tends to focus on impacting three major components of these types of networks: controllability, observability and operability (known as the “CO2 framework”).
Of the three, operability attacks are the most directly physically damaging. However, compromising any of the CO2 factors may contribute to physical damage, or to a level of disruption that may become damaging if sustained.
………………………..

 by
by