Overview
Ransomware is no longer a marginal cyber risk. It has become a systemic threat, driven by the rapid expansion of cloud infrastructure, widespread AI adoption, and growing dependence on third-party technology providers. Organisations across every major sector now operate in highly connected digital ecosystems where a single weak link can expose thousands of downstream users.
Public leak sites, deepfake-enabled fraud, and supply chain attacks have shifted the economics of cybercrime, making disruption faster, louder, and harder to contain.
Recent data from QBE and Control Risks shows how quickly the threat profile is changing. Beinsure analyzed the cyber trends and highlighted the key points.
- Ransomware victims continue to rise, cloud environments generate record levels of high-severity alerts, and sensitive data concentrates in fewer platforms.
- Governments, infrastructure operators, and technology providers face the highest pressure, but private companies are not insulated.
- Insurance markets are tightening, loss ratios are climbing, and underwriters demand far deeper insight into security practices than in the past.
This research examines how cloud adoption, AI tools, and supply chain complexity are redefining cyber risk, and why resilience now depends on preparation rather than recovery.
Ransomware attacks are set to rise sharply
Ransomware attacks are set to rise sharply, with victims publicly named on leak sites expected to climb from 6,000 in 2025 to more than 7,000 by the end of 2026. The jump marks a fivefold increase since 2020, when only 1,412 victims appeared on those sites.
The UK accounts for a meaningful slice of the problem. Over the past two years, the country recorded 49 significant cyber incidents, about 10% of the global total of 447.
That concentration puts Britain high on the risk map, even by European standards. The findings come from QBE’s cyber report, Cloud cover: forecasting digital disruption in a cybercrime climate, compiled by Control Risks.
The report explains how attackers exploit weaknesses tied to cloud adoption and AI use to reach sensitive data and disrupt operations.
Key findings
- Ransomware incidents nearly tripled year over year. Q1 2025 logged 1,537 cases, up from 572 in Q1 2024, a jump that tracks both attacker confidence and weaker defensive gaps at scale.
- Cloud risk escalated even faster. High-severity cloud alerts surged 235% in 2024 versus 2023, reflecting aggressive cloud adoption alongside sharper attacker tactics. Almost half of all corporate data stored in the cloud now qualifies as sensitive, which makes those environments an obvious target for extortion.
- Global data volume is expected to hit 200 zettabytes by 2025. About 50% will sit in the cloud, up from 43% in 2024 and just 15% in 2020. Concentration keeps rising. So does exposure.
- Deepfakes moved from novelty to tool. They appeared in nearly 10% of successful cyberattacks in 2024, with fraud losses ranging from $250k to more than $20 mn per incident. Speed and realism changed the economics of scams.
- Ransomware extortion disclosures also accelerated. Publicly named cases rose 54% between January and April 2025 compared with the same stretch in 2024. Attackers want visibility. Pressure works better that way.
AI adoption keeps reshaping the field. ChatGPT reached 755 mn users in early 2025, up 33% between December 2024 and February 2025. Microsoft Copilot reported 88 mn users. About 78% of organisations now deploy AI in at least one business function, up from 55% a year earlier. Between 20% and 40% of employees actively use AI in daily work, especially in programming roles, according to Beinsure’s research.
Operational risk showed up in a different form in 2024, when a CrowdStrike outage disrupted 8.5 mn Windows devices. The incident cost Fortune 500 companies an estimated $5.4 bn, a reminder that defensive tools can become systemic risks when something breaks at scale.
Cyberattacks target governments and core infrastructure at global scale

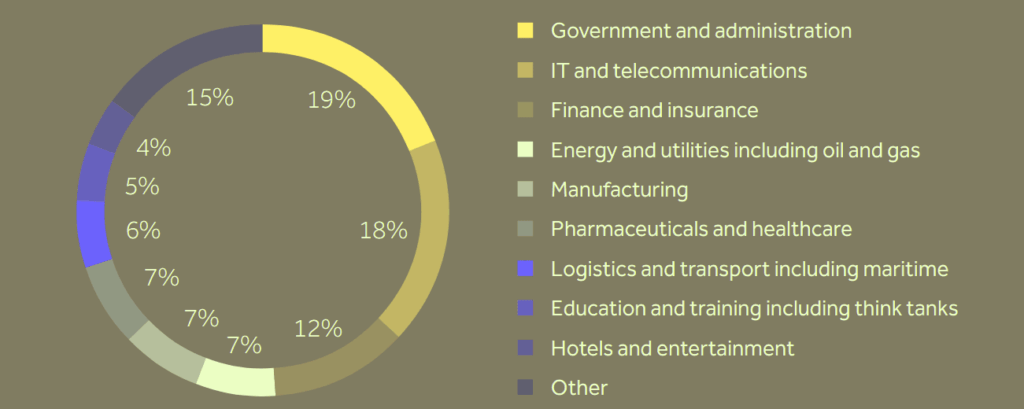
Government and administrative bodies emerged as the most targeted sector worldwide between August 2023 and August 2025, representing 19% of all incidents. IT and telecommunications followed at 18%. Manufacturing, logistics, and transport combined accounted for 13%. The spread shows how attackers chase scale and dependency rather than niche targets.
Ransomware attacks bring more than direct financial loss. They trigger reputational damage, regulatory scrutiny, and litigation risk, not just for the victim but for customers and third-party suppliers tied into the same systems.
According to Beinsure analysts, that knock-on exposure keeps widening as ecosystems grow more connected.
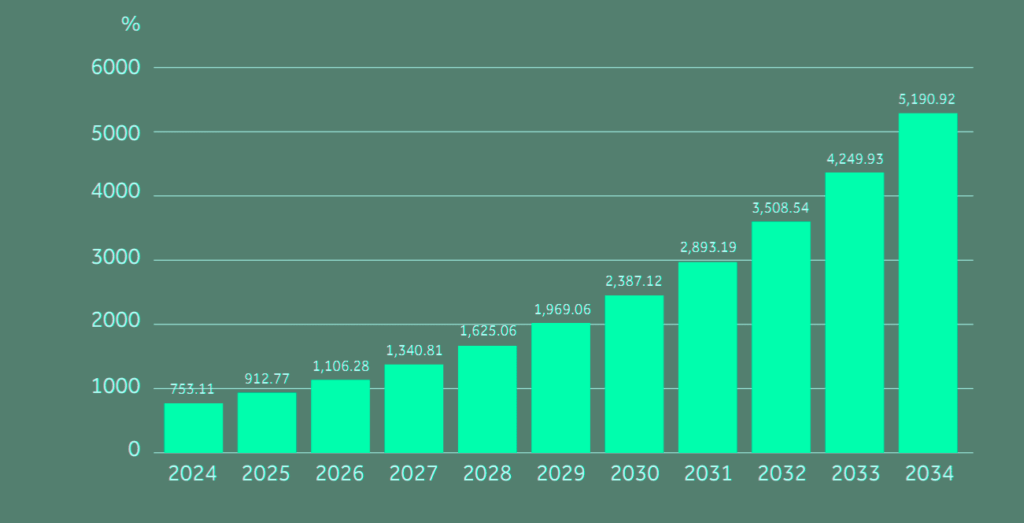
Total number of projected ransomware victims named on leak sites
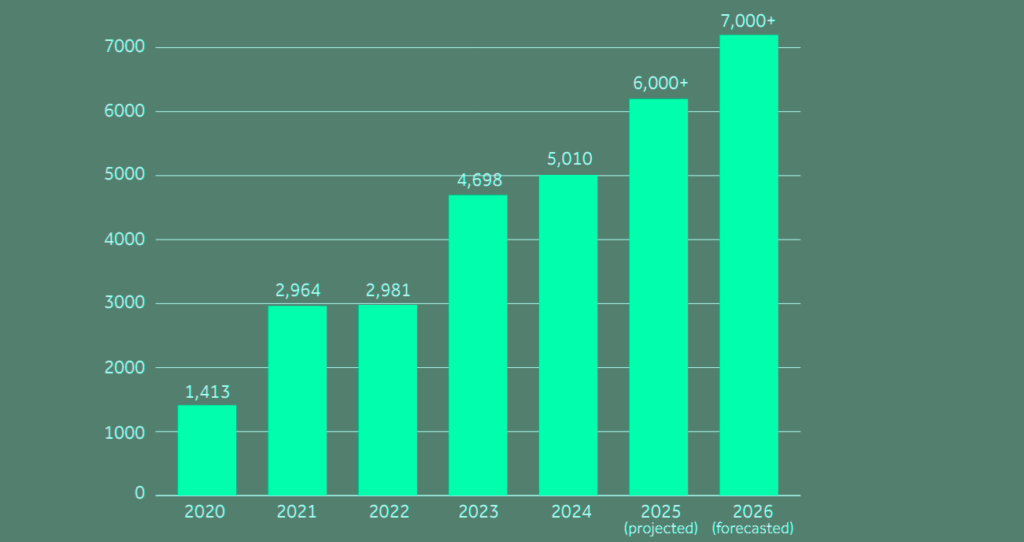
Projected ransomware exposure
| Metric | 2020 | 2024 | 2025 | 2026 (proj.) |
| Victims named on leak sites | 1,412 | 5,010 | ~6,000 | >7,000 |
| YoY change | – | – | +20% (est.) | +15%+ |
| Multiple vs 2020 | 1.0x | 3.5x | 4.2x | 5.0x |
Number of significant cyber incidents recorded by geography
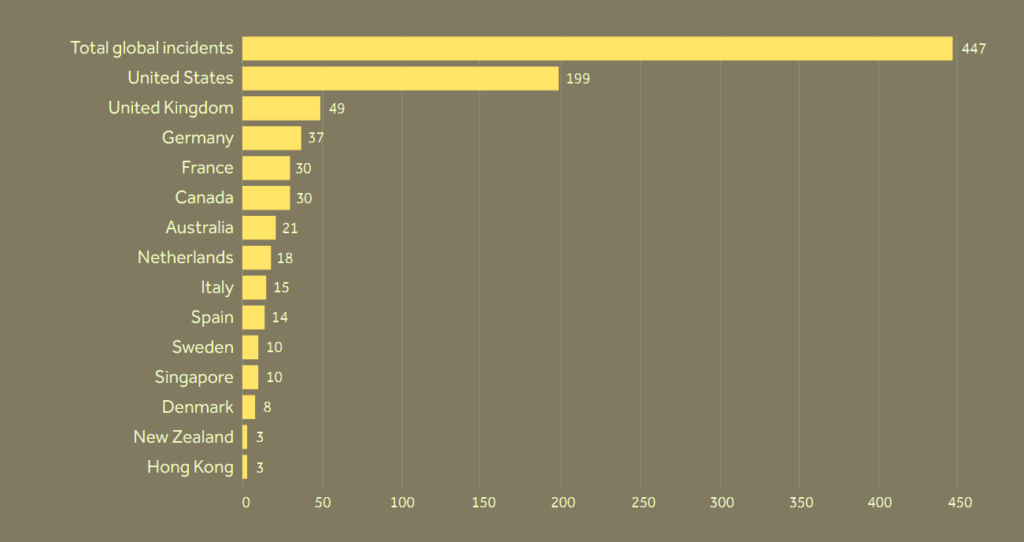
Significant cyber incidents by geography
| Geography | Incidents | Share of global total |
| Global total | 447 | 100% |
| UK | 49 | ~10% |
| Rest of world | 398 | ~90% |
Ransomware attacks are on the rise in the United States and local counties are scrambling to keep their cyber systems insured. For those who lack cyber protection, the price can be both costly and time-consuming.
Ransomware evolution and insurance impact
| Period | Threat Evolution | Claims Characteristics | Estimated Insured Losses |
| 2015–2017 | Data breaches dominate; opportunistic ransomware | Quick resolution, modest severity | <$100mn annually |
| 2018 | RaaS & cryptocurrency adoption; un-targeted ransomware | Volume-driven, rising severity | ~$300mn annually |
| 2018–2019 | “Big-game hunting” targeting large orgs | Higher ransoms ($500k–$3mn) | $500mn+ annually |
| 2020–2021 | Double extortion (encryption + data theft) | Longer-tail exposures, regulatory costs | $5–7bn annually |
| 2022–2023 | Supply chain & critical infrastructure targets | Systemic risk; stricter underwriting | $5–8bn annually |
| 2024–2025 | Stabilization & risk differentiation | Frequency declines, severity remains high | $4–6bn annually |
During the 2019 Baltimore Ransomware Attack, the city of Baltimore was targeted by a variant of ransomware called Robbinhood, Beinsure noted. As a result, the majority of the city’s essential servers were immediately shut down.
In order to reverse the damage, hackers demanded 13 bitcoin. If the city failed to pay the ransom, the amount would increase, as would the intensity of the shutdown.
Ultimately, the city refused to pay the ransom and the total cost of the attack far exceeded the initial amount requested by the hackers. Throughout the event, the city struggled to maintain its systems.
Globally, organisations face the growing risks of operational downtime, financial loss and reputational damage as criminals exploit an expanding attack surface.
Cyber incidents affecting key markets, by sector
The increasing use of third-party services such as cloud-hosting, external software or AI tools in day-to-day operations has given threat actors more opportunities to strike.
Cyber incidents by sector
| Sector | Share of incidents |
| Government & administrative | 19% |
| IT & telecommunications | 18% |
| Manufacturing, logistics & transport | 13% |
| Other sectors | 50% |
The Real Estate Accounting and Services Division was heavily impacted as it housed systems for tax collection, title fees, and even water bills.
In aggregate, the loss ratio on US cyber insurance rose from 44.6% in 2019 to 73% in 2024, with ransomware accounting for three quarters of claims according to AM Best.
While the bulk of ransomware claims reflect recovery and remediation costs from an attack, including business interruption, the share associated with the reimbursement of ransoms has increased. More recent indicators suggest no material improvement in the claims environment, with ransomware remaining a key driver.
Cyber insurance pressure indicators (US)
| Metric | 2019 | 2024 |
| Cyber insurance loss ratio | 44.6% | 73% |
| Share of claims from ransomware | – | ~75% |
| Insured losses (annual) | < $100 mn | $4–6 bn |
Gone are the days when a county could merely answer a few questions to receive cyber insurance. Today, insurance carriers require an in-depth and bottom up understanding of a county’s security practices and protocols.
According to Gallagher’s Cyber Report, last year was a stark reminder that hackers are pivoting in deploying new attack strategies. There is clear evidence that they now favor targets in the supply chain that could provide a gateway to multiples of additional victims, providing efficiencies to their methods.
QBE is urging companies to strengthen controls as threats change shape. David Warr, cyber portfolio manager at QBE, said British firms expanding cloud infrastructure and AI tools are also reshaping their risk exposure.
As British businesses expand their use of cloud infrastructure and AI tools, they are also reshaping their risk landscape. The challenge is not just preparing for the future but catching up with exposures that have evolved at speed. The supply chain threat causes concern for companies.
David Warr, Cyber Portfolio Manager for QBE
“While outsourcing certain parts of your business can create efficiencies and cost savings, there are security considerations to bear in mind. Each outsourced provider that connects into your company creates an additional layer of risk – not only in terms of potential malware transmission but also in terms of critical dependencies. Each third-party connection creates new risk, and a single point of failure can halt business operations altogether,” David Warr says.
He warned that supply chain connections remain a weak spot. Each outsourced provider adds another access point, another dependency, another way operations can grind to a halt if one link fails.
Rapid adoption of AI and cloud platforms

AI adoption and cloud platform capabilities are transforming business – but the speed and scale of such a rapid shift provides rich opportunity for ransomware, fraud and third-party disruption.
Rapid adoption of AI and cloud platforms increases digital exposure. These tools lift productivity, yet they also give attackers speed and precision.
In 2025, deepfakes featured in nearly 10% of successful cyberattacks, with losses ranging from $250,000 to more than $20 mn. Fraud has learned to scale.
By 2025, global data storage is projected to reach 200 zettabytes across IT systems, utilities, data centres, and connected devices, Beinsure says. About half of that data will sit in the cloud, up from 10% in 2015. Concentration attracts attention. Attackers follow value.
A proactive, cyber resilience-first approach is essential
Businesses must embed risk management into their technology systems, anticipate third-party vulnerabilities and build continuity planning into their operations.
The scale of cloud adoption underscores the urgency in moderating this exposure. The global market is expected to exceed $5 tn by 2034, up from $912 bn in 2025.
Projected value of global cloud computing market by year ($ bn)
As more organisations transfer infrastructure and data to the cloud servers, those servers become high-value targets. High-severity cloud alerts increased by 235% throughout 2024 compared with the previous
year, reflecting both the surge in adoption and the increasing capability of attackers.
Ransomware activity acceleration
| Metric | Q1 2024 | Q1 2025 | Change |
| Ransomware incidents | 572 | 1,537 | ~2.7x |
| Public extortion disclosures (Jan–Apr) | Baseline | +54% | Sharp increase |
The Geneva Association report highlights the important role of private re/insurers, alongside governments, in boosting society’s resilience to ransomware and ensuring the full benefits of digitalisation can be realised.
During 2024, high-severity cloud alerts jumped 235% year over year. Adoption accelerated. Attacker capability did too.
Cloud platforms now serve as a common entry point, especially through business email compromise attacks that abuse Microsoft 365 and similar services.
These attacks often slip past older security controls and stay hidden longer.
AI adoption and cyber impact
| Indicator | 2024 | 2025 |
| Organisations using AI | 55% | 78% |
| Employees actively using AI | – | 20–40% |
| ChatGPT users | – | 755 mn |
| Microsoft Copilot users | – | 88 mn |
| Attacks involving deepfakes | ~10% | ~10% |
| Typical deepfake fraud loss | $250k | >$20 mn |
Many ransomware victims may simply find it easier and less costly to pay the ransom demand than to endure interruption to their businesses and/or incur costs to remove the malware and restore data. This is potentially creating a vicious cycle and incentivising criminals to continue carrying out ransomware attacks.
A natural reaction may be to prohibit ransom payments altogether; some governments around the world contemplate such a move. But the law of unintended consequences suggests caution, as such a ban could mean that organisations most in need of protection are even more exposed to an attack.
Business leaders are aware of AI-driven cyber risks and their implications

But understanding changing risk profiles to make better decisions around the management of new exposures is the key to cyber resilience, according to Aon report.
The global threat landscape has shifted rapidly, with AI-powered cyber threats becoming more advanced and frequent.
Yet, only 30% of surveyed organizations hold cyber insurance, leaving many exposed to avoidable financial losses.
As technology evolves, particularly through AI, new risks emerge, requiring both awareness and updated approaches to cyber risk management, including ongoing changes in insurance coverage.
Cloud risk concentration
| Indicator | 2015 | 2020 | 2024 | 2025 (proj.) |
| Share of global data in cloud | 10% | 15% | 43% | ~50% |
| Global data volume (zettabytes) | – | – | – | 200 |
| High-severity cloud alerts | – | – | +235% YoY | Elevated |
According to Beinsure’s data, with over 600 mn cyber attacks occurring daily, the global threat environment has shifted dramatically.
AI-powered threats – ranging from phishing and malware to sophisticated social engineering – are increasing in frequency and impact.
Alongside this, state-sponsored actors, cyber crime syndicates, and hacktivist groups continue to fuel a volatile digital risk landscape.
Projected monthly numbers of ransomware victims named on data leak sites
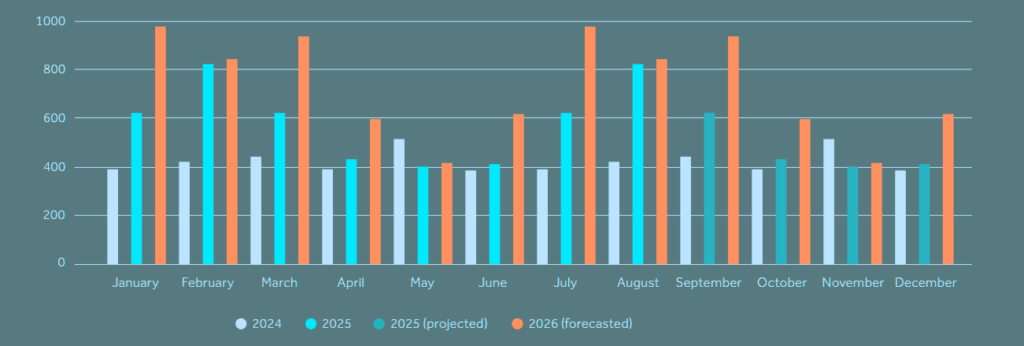
Insurers have responded with broader cyber coverage, offering policies that address ransomware, data breaches, and operational disruption.
Yet, most companies remain unprepared to fully quantify their risk exposure or align coverage with current digital realities.
According to Global Cyber Risk Report, third-party risk continued as a frontline issue across the year, as businesses found it increasingly challenging to protect their supply chains.
And importantly, we observed occasional misunderstandings about what cyber insurance covers – and doesn’t cover – which reflects the need for more education across the industry.
Global competition in the cyber insurance sector increased, and pricing for US-based risks declined for the tenth consecutive quarter.
Supply chain exposure continues to grow
A breach at single sign-on provider Okta in 2023 exposed 134 business clients and erased roughly $2 bn from its market value. One supplier failed. Hundreds of companies paid the price.
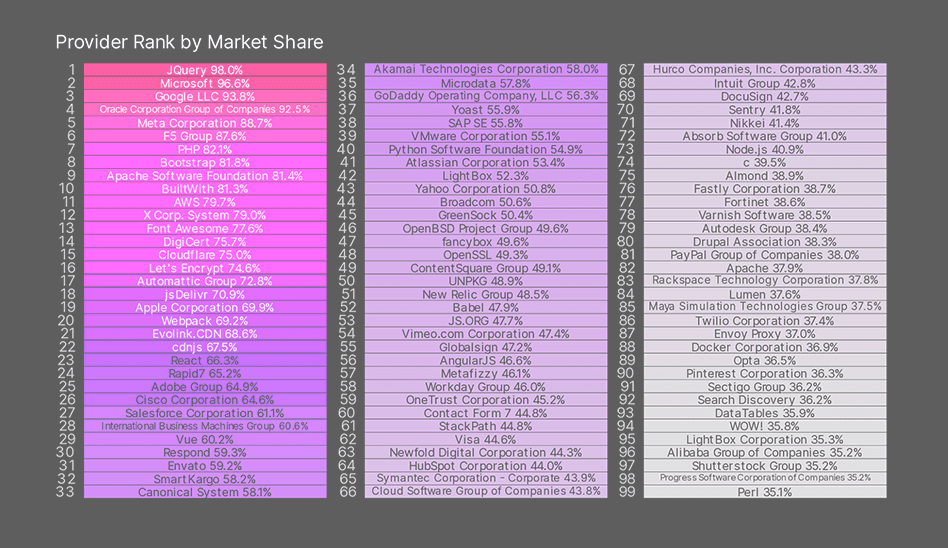
A Bitsight’s research report, Under the Surface: Cybersecurity Risks within the Global Supply Chain, lays out a blunt picture of how exposed modern supply chains really are.
Supply chains sprawl wider than most companies realise. A typical organisation runs on hundreds of products sourced from dozens of vendors, each one adding another dependency and another risk point.
Providers carry an even heavier load. The data shows they operate supply chains about 2.5x larger than those of the customers they support. That scale expands the attack surface fast, and providers, on average, struggle more than their consumer clients to keep defences tight.
Attacks on cloud environments, by initial access vector
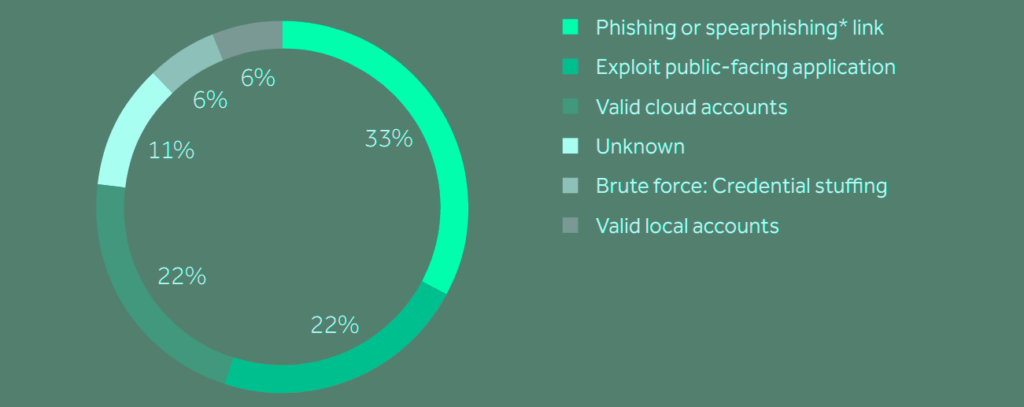
By 2025, the volume of data stored worldwide is projected to reach 200 zettabytes (200 tn gigabytes) across private and public IT infrastructures, utility infrastructures, private and public cloud data centres, personal devices and internet of things (IoT) devices.
Half of this data will be stored in the cloud, compared with 43% of data stored in the cloud in 2025, an estimated 15% in 202015 and only 10% in 2015.
This concentration of valuable data makes cloud providers and storage services appealing to attackers.
Supply chain concentration risk
| Indicator | Value |
| Orgs using DoD-listed Chinese Military Companies (US) | 33% |
| Avg. products per organisation | Hundreds |
| Avg. vendors per organisation | Dozens |
| Provider supply chains vs customers | ~2.5x larger |
| Vendors serving <1% of firms but >50% revenue | Common |
| “Critical 99” providers | 99 firms |
Risk also clusters in uncomfortable ways
In several industries, vendors serving less than 1% of companies control more than 50% of total market share when measured by client revenue. A small failure zone. Massive downstream exposure.
Cyber threat actors’ tactics, techniques, and procedures (TTPs) are constantly evolving, exposing cyber insurers to an ever-changing loss mix. Annual insured losses surged from under $100 mn pre-2017 to $4-6bn by 2025.
The shifting claims environment requires insurers to regularly re-evaluate development patterns to accurately assess performance and rate adequacy.
Geopolitics enters the picture too
About 33% of U.S. organisations rely on companies listed by the U.S. Department of Defense as Chinese Military Companies. In the current climate, understanding exactly who sits inside your supply chain isn’t optional. It’s basic risk hygiene.
The report also identifies the “Critical 99,” the top 99 providers globally by market share. These firms act as quiet load-bearing beams for large segments of the global economy, supplying services that support a disproportionate share of industry revenue. Many operate out of sight. None are low impact.
Critical 99 in the global supply chain
Generative AI is adding fuel
Use across Europe and North America is expected to surge over the next five years.
- ChatGPT now counts 755 mn users, up 33% between December 2024 and February 2025.
- Microsoft Copilot reports 88 mn active users in 2025.
- 78% of organisations deploy AI in at least one business function this year, up from 55% in 2024.
Systemic technology failure example
| Event | Impact |
| CrowdStrike outage (2024) | 8.5 mn Windows devices affected |
| Estimated Fortune 500 losses | ~$5.4 bn |
| Risk type | Defensive tool failure at scale |
Businesses use GenAI to move faster. Attackers use it to automate phishing, sharpen fraud, and run deepfake scams at scale. The tools are neutral. The outcomes are not.
GenAI enables hackers to act with greater speed and precision, but it also lowers the technical barriers for entry-level cybercriminals, for instance assisting them in script development and malware coding.
Businesses will likely face a rise in attacks from groups previously dismissed as too technically incompetent or resource-poor. This may result in operational downtime, financial loss or reputational damage.
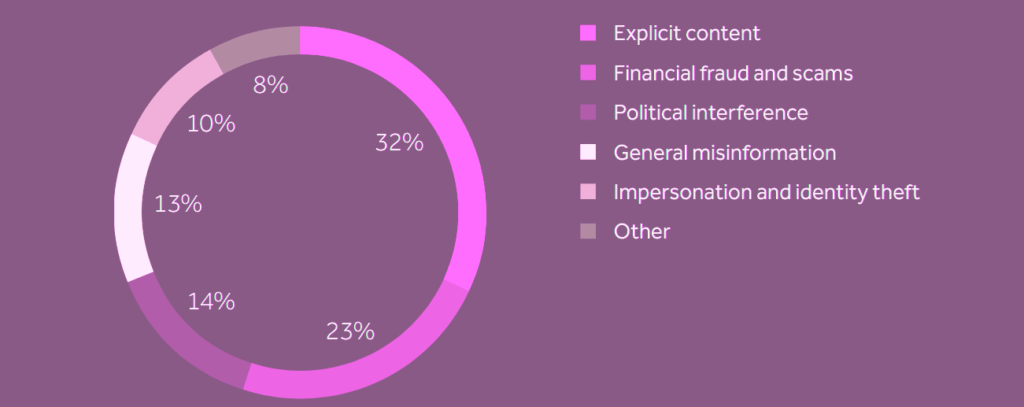
Content type of deepfake attacks
Cloud and AI tools are giving attackers more entry points and opportunities. Businesses need a robust strategy to anticipate and withstand cyber incidents, particularly those arising from third-party services and cloud environments.
Building resilience means embedding cyber risk management into technology lifecycles from the outset:
- Implementing strong identity and access management (IAM) protocols
- Running regular configuration audits
- Encrypting sensitive data across all cloud environments
Building resilience means embedding cyber risk management into technology lifecycles. This involves strong identity and access management protocols, regular configuration audits, and sensitive data encryption.
Also, continuous monitoring, threat intelligence, and incident response plans help detect and contain threats before they escalate.
In addition, businesses should evaluate the security posture of their third-party providers and establish clear protocols for managing supply chain exposure.
FAQ: ransomware, cloud risk, and cyber insurance pressure points
Attackers now combine cloud access, AI tools, and supply chain entry points to scale faster and hit multiple victims at once. Public leak sites amplify pressure, making extortion more effective and repeatable.
The UK recorded about 10% of global significant incidents over the past two years because of high cloud adoption, dense digital supply chains, and heavy reliance on third-party services across public and private sectors.
Nearly half of corporate cloud data is classified as sensitive, and by 2025 around 50% of all global data will sit in the cloud. Concentration creates value. Attackers follow value.
AI speeds everything up. Deepfakes now appear in almost 10% of successful attacks, phishing campaigns scale automatically, and entry-level attackers can generate malware and scripts they couldn’t build before.
Government, IT, telecoms, and transport offer scale and dependency. One breach disrupts services for millions, which raises leverage and visibility for attackers looking to force payment.
Most organisations rely on dozens of vendors, while providers run supply chains about 2.5x larger than their customers. A single compromised supplier can expose hundreds of downstream firms in one move.
Loss ratios climbed sharply as ransomware claims dominate, and insurers now demand detailed proof of security controls, cloud governance, and third-party risk management before offering coverage or capacity.
……………….
AUTHOR: David Warr – Cyber portfolio manager at QBE Europe. Edited by Peter Sonner – Lead Tech Editor at Beinsure Media