Overview
In response to uncertainty around cyber risk, insurance providers have become more selective in their underwriting through better risk selection, lower limits, cyber insurance and tighter policy terms.
As insurers reduce portfolio sizes and exposures, market growth might face upper bounds. This could leave the economy more exposed to cyber threats and affect societal resilience.
By reducing uncertainties, risk carriers can increase the insurability of cyber exposures and improve the growth potential of the cyber insurance market.
In this section, we focus on enhancing insurability by improving risk knowledge through data and modelling, and increasing clarity around catastrophic losses.
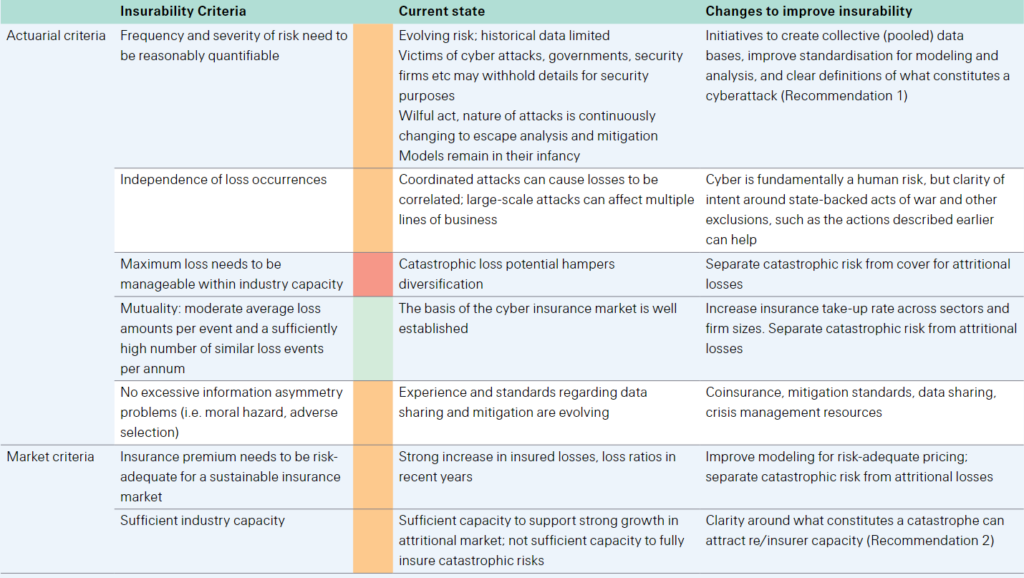
Main types of cyber loss estimates
Improving risk knowledge to reduce pricing uncertainty
When there is a high degree of uncertainty around average expected losses, insurers tend to restrict coverage. To this end, reducing uncertainty with data and improved modelling capacity can expand the coverage available in the market. Cyber risks are difficult to quantify due to a lack of standardised data and modelling constraints within a shifting risk environment.
Actuaries typically infer future risks based on backward-looking data, but this approach is limited in the context of cyber risk for two reasons:
- a lack of standardised data
- backward-looking information is less useful in a rapidly changing risk environment.
Capturing and analysing better data is critical for probabilistic modelling and developing reliable loss estimates to better understand the dynamics and implications of cyber losses. This requires detailed knowledge of the range of risks, their impacts and the reliability of data.
The introduction of cybersecurity standards can also reduce uncertainty about potential losses.
Private-sector attempts to address these shortcomings include the establishment of CyberAcuView, a consortium of leading cyber insurers to collect cyberattack and claims data, and to develop cyber data information standards.
In Europe, the insurance and reinsurance federation is taking steps to facilitate access to standardised and anonymous breach data collected under GDPR.
There is increasing scope for coordination between the public and private sectors as well. For example, the US Cyber Incident Reporting for Critical Infrastructure Act was signed into law in March 2022, which will require critical infrastructure operators to report “substantial cyber incidents” to the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency within 72 hours and ransomware payments within 24 hours.
Even as the cyber insurance market matures and additional data become available, developing accurate loss estimates will remain challenging given the evolving nature of the risk.
New technologies, motives, threat actors and attack methods make the past a weak guide to the future, as underlying loss distributions change faster than those of more traditional lines.
These characteristics of cyber risk bring both probabilistic and scenario models into play with limitations for either concept.
Data for individual clients will not be sufficient for risk assessment and need to be complemented by larger industry data pools. This requires a modelling landscape that is capable of adopting new analytic methods including artificial intelligence (AI) and machine learning (ML). The dynamic nature of such models also means they require more model governance (ie, performance monitoring, data review and benchmarking).
To date there has not been a true cyber catastrophe event, so scenario estimates are instructive for the purpose of giving a sense of scale, emphasising the potential for risk accumulation and aggregate levels of cyber risk, and ultimately giving risk carriers confidence to allocate additional capacity to the sector.
Acts of cyber warfare, the disruption of a cloud provider of critical software or the deployment of malware through commonly-used software are examples of scenarios that could generate catastrophic losses. Re/insurers and analytics firms continue to enhance proprietary scenario estimates, which will improve with data standardisation and experience with cyber events.
To remain current on an evolving risk, technology firms and re/insurers must also continually work to develop greater cyber expertise in the work force. As a recent example, in October 2021 Microsoft unveiled an initiative to fill the cybersecurity skills gap by providing access to free a curriculum and teaching tools.
Re/insurers can also help to tackle the cyber talent shortage by strengthening partnerships with universities to develop education programmes relevant to their business. This would include cyber risk modelling and forensic analysis to strengthen the actuarial and technical skills needed for the underwriting and claims management cycles.
Underwriting actions and data standardisation can help insurers manage attritional losses,84 but available capacity in cyber is also impacted by potential extreme events that are much more capital-intensive. Greater confidence in cyber catastrophe risk modelling and clarity around what constitutes a catastrophic loss can improve insurability and attract more capacity to the cyber insurance market.
Main types of cyber loss estimates
| Type | Description | |
| Bottom-up analysis | Rely on statistical microdata (eg, individual cyber incident claims data), typically used | |
| in actuarial analyses to assess risk. | ||
| Aggregate estimates | Typically used by cybersecurity vendors to show the need for investment in | |
| (national/global scale) | cybersecurity. | |
| Scenario estimates | Emphasise extreme events and the potentially devastating magnitude of the resulting | |
| losses. |
Aggregation risk connects public and private sector concerns
Some potential cyber scenarios might reduce available capacity. For example, in 2015 Lloyd’s estimated that a widespread cyberattack on the US power grid could cause up to USD 1 trillion in economic damage and USD 71 billion in insured losses.
The fallout from this type of attack includes a rise in mortality rates, decline in trade, and disruption to supplies and transportation networks. Aggregation risk links national security and critical infrastructure vulnerabilities with private markets. National defence is the government’s priority while the private sector typically owns large parts of the critical infrastructure that is vulnerable to attacks.
Collaboration between the public and private sectors to address cyber threats to infrastructure can expand insurability by mitigating the risk and reducing uncertainty about the response to cyber catastrophes.
A cyberattack on critical infrastructure could have cascading impacts across the economy. Beyond economic damages, a successful attack could erode public confidence in utilities and the financial system.
The public and private sectors are working together to identify critical assets and define responsibilities for maintenance, provision of services and the implementation of response protocols.
Addressing aggregation risk via policy language standardisation
The relative youth of the cyber insurance market and complexity of the risk are reflected in a lack of standardisation around exclusion clauses and terms and conditions. The potential for catastrophic events stemming from state-backed acts of war, hostile cyber acts or critical infrastructure failure – and a lack of clarity regarding the ensuing liability – is an important factor curtailing capacity in cyber insurance.
Scenario estimates of cyberattacks with insured losses in the tens of billions of dollars are many multiples of insurance premiums, and modelled economic losses are much greater.
Developing a uniform approach to deal with aggregate losses can support sustainable growth by creating better-understood solutions for corporations and bolstering the risk appetite of insurers.
Associations, individual insurers and think tanks have taken steps to standardise definitions for cyber war, operations and attribution. In November 2021, the Lloyd’s Market Association introduced clauses designed to exclude coverage for cyber war and cyber operations, with a requirement that these or similar exclusions are applied from 31 March 2023.
The significance of Lloyd’s bulletins extends beyond the direct marketplace since the exclusions must fit into any reinsurance tower that Lloyd’s syndicates are involved in and thus have implications for all re/insurers in the same programme.
Attribution is a core problem. Insurers are adopting differing approaches
But a coordinated approach remains aspirational. A fundamental problem for coverage determinations is that a simple technical process for attributing cyber operations does not exist. Some observers suggest that carriers avoid the Lloyd’s exclusions, and a couple of insurers in the US are creating their own exclusions to address catastrophic cyber events.
Chubb has created endorsements to tailor coverage for widespread events, ransomware encounters and neglected software vulnerabilities, providing a framework for pricing catastrophic risks and evolving vulnerabilities.
And Beazley is updating its exclusions for cyber war and infrastructure failure while placing sub-limits around catastrophic cyber events that have a “major detrimental impact” on the functioning of a state.
Earlier reports provide a basis for consideration in moving towards a common language and provide insights to help evolve industry policy language. For example, in 2020 the Geneva Association proposed the term “hostile cyber activity” to describe cyber acts that fall between war and terrorism, while the Carnegie Endowment proposed using two complementary exclusions to deal separately with catastrophic and war-related or state-sponsored cyber risks. Some companies expect to see more of these cat/non-cat rather than war exclusions.
Insurers have taken steps to address silent cyber exposures
The cyber insurance cover described in this report is “affirmative”, as perils are explicitly included or excluded. “Silent cyber” is a related topic, encompassing cyber perils that are not explicitly listed in traditional policies, although policy holders may still assert claims.
This can lead to significant losses for insurers despite not intending to provide cyber coverage. The best-known example to date is the NotPetya attack in Ukraine.
Despite being a cyberattack, approximately 85% of insurance industry loss was reportedly through property claims that did not explicitly include or exclude cyberattacks.
Exposure to silent cyber can be mitigated by making cyber exposures explicit – either pricing for cyber in packaged (non-cyber) policies, or shifting the risk into standalone policies. Better risk evaluation and more accurate pricing will improve the sustainability of the market.
Insurers have taken steps to address silent cyber risks, updating policies and beginning to standardise wording, exclusions and endorsements. For example, in November 2019, the Lloyd’s Market Association (LMA) introduced clauses to address silent cyber exposures in property and marine insurance.
Adding capacity with non-traditional risk-carriers
One option for addressing part of the protection gap that results from hard-to-model and non-diversifying tail risks is to develop a market for cyber insurance-linked securities (ILS). Currently, it is estimated that alternative capital will provide around USD 95 billion additional catastrophe reinsurance capacity in 2022, supplementing dedicated traditional reinsurance capital of USD 435 billion.
There is latent interest in growing alternative capital solutions for cyber risks to support a sustainable cyber market. To date, however, ILS investor interest has been limited, with aggregation risk and model uncertainty acting as main deterrents.
True ILS structures (akin to cat bonds) require the development of objective triggers, which could present the insured with considerable basis risk. Alternative capital managers are investing in cyber insurtech companies to improve the understanding of the risk and to potentially deploy capital to support it.
Meanwhile, indemnity-based third-party capital structures, such as re/insurance sidecars, can bring new capacity to cyber underwriters.
Another potential solution to help close the protection gap is to design a type of public-private partnership (PPP) insurance scheme, where the coverage of systemic risks is split between insurers and a government(s)-backed fund. In the US, the Government Accountability Office has recommended that the Cybersecurity and Infrastructure Security Agency and the Federal Insurance Office produce a joint assessment on the extent to which catastrophic cyberattacks on critical infrastructure warrant a federal insurance response.
The ultimate form this could take, including structure, funding, participation requirements and scope of coverage remains to be determined and is being assessed by policymakers at the US Treasury and in other jurisdictions.
The global cyber protection gap is estimated to be at around 90%
The cyber risk landscape is rapidly evolving and, as cyberattacks have increased, so too has awareness of the risk and demand for cyber insurance solutions.
Most businesses and individuals are uninsured or significantly under-insured for cyber exposures, and cyber insurance premiums amount to just a fraction of total losses from cyberattacks. Estimates put the cyber protection gap at 90%.
This points to the large growth potential for the insurance market, but there is much work to do to ensure sufficient risk protection is available to make society more resilient to cyber risk. And this effort will require collaboration between businesses, the insurance industry and government.
……………………
AUTHORS: Elena Jelmini Cellerini – Senior Claims & Key Case Expert Swiss Re, James Finucane – Senior Economist, Dr Thomas Holzheu – Head of the Swiss Re Institute for the Americas