Overview
- Banning ransom payments is a blunt, potentially ineffective instrument
- Cyber insurance provides more than cover for ransoms
- Involving experts leads to better outcomes for the insured
- Insurance helps improve overall cyber hygiene standards
- How cyber insurance helps policyholders confront a ransomware attack
- Governments and regulators must go further to counter ransomware attacks
- Recent government-led initiatives to counter ransomware
The views of the insurance industry are not always prominent in the debate on ransomware. In order to provide a re/insurer perspective, we surveyed selected insurance companies that are active in cyber insurance.
The Geneva Association report highlights the important role of private re/insurers, alongside governments, in boosting society’s resilience to ransomware and ensuring the full benefits of digitalisation can be realised. Report summarises and synthesises the results of a short questionnaire and/or interviews with cyber experts at 15 re/insurers, which collectively account for a major share of the global cyber insurance market.
Banning ransom payments is a blunt, potentially ineffective instrument
All respondents recognise the significant challenges posed by cybercrime and ransomware in particular (see Largest Ransomware pay-outs by Cyber Insurers).
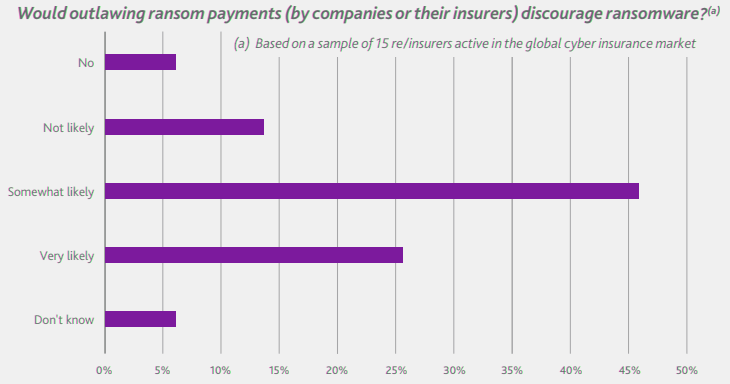
While there is no overall consensus, most feel that banning ransom payments by the targeted companies or prohibiting reimbursement by re/ insurers would probably discourage ransomware attacks to some degree, at least against smaller firms with fewer resources.
Most re/insurers feel that banning ransom payments or prohibiting their reimbursement would probably discourage some ransomware but that it is a blunt policy response that may not always have the desired effect.
However, they also point out that such a blunt policy response may not always have the desired effect, especially if bans are not consistently applied on an international level.
A ban solely against insurer reimbursements would be particularly ineffective, depriving victims of an important means of protection when other forms of risk financing may be difficult to organise.
The absence of cyber insurance cover for extortion payments not only penalises the insured, but also does nothing to address the growth of RaaS, which has fuelled ransomware attacks.
Re/insurer views on a ransom ban
Italy’s experience with K&R in the 1990s underscores the challenges of any ransom ban. The Italian government made it illegal to pay ransoms in 1991, a move widely credited for the subsequent flattening in kidnapping rates.
But the threat did not go away completely as the families of kidnapped Italian citizens simply stopped reporting crimes to authorities.
If ransomware payments were outlawed, victim companies would likely look to cover up attacks and route ransom payments through unofficial mechanisms to avoid detection.
This potentially means that learnings and lessons about new ransomware strains would largely go unheeded.
Cyber insurance provides more than cover for ransoms
Insurance plays an important role in supporting companies to absorb ransomware-related losses, including privacy/data breaches, business interruption, recovery of data and systems, forensics and legal assistance.
While ransom payments often grab the headlines, the losses related to a ransomware attack go well beyond extortion demands. Insurance plays an important role in supporting companies to absorb a variety of first- and third-party losses resulting from ransomware.
After an attack, cyber insurance can serve as a mechanism for convening the right team of experts, including legal counsel and computer forensic analysts, to assess the incident and recommend a timely response.
Cast in that light, most re/insurers are not daunted by the prospect of a ban on ransom payments as the value proposition of cyber insurance would remain. In fact, cyber coverage could become even more valuable to the insured given the potentially higher recovery and remediation costs compared with paying a ransom.
As well as any downtime, these costs could stem from the need to restore lost or corrupted data/information or manage any reputational fall-out and third-party liabilities from a data breach.
Adjusting the scope of cover offered will be easier in some markets than others. In the U.S., the most mature cyber insurance market, there could be initial pushback from customers who recognise that they operate in the most targeted country for ransomware attacks. According to the latest Zurich/Advisen survey of U.S. companies, 95% of respondents expect cyber extortion coverage to be included in their policies, on par with protection against data breaches.
Yet recent steps to restrict coverage – including increased participation in out-of-pocket expenses via co-insurance as well as reduced policy limits for ransoms – have been absorbed by the market, suggesting strong underlying demand for protection. Similarly, companies still derive value from their cyber insurance in markets where ransom payments are normally not covered, for example in Japan.
Involving experts leads to better outcomes for the insured
Most re/insurers believe involving independent experts in the response to ransomware attacks helps the affected organisations make informed decisions, especially in areas where they have little experience.
Experts also bring in negotiating skills that can be used to help lower the ransom actually paid – not least because they are well placed to assess the credibility of the threat, including the viability of decryption keys and likelihood of restoring operations. Consistent with that, the ratio of average ransoms paid to initial ransom demands has reportedly declined, despite increased efforts by criminals to leverage data exfiltration and other methods to extort their victims.
The use of specialist intermediaries can also reduce operational frictions associated with a ransomware attack, such as ensuring the ransom recipient is not subject to criminal or anti-money laundering sanctions, reporting the incident to the relevant authorities and sourcing cryptocurrency to facilitate payment.
Moreover, ransom brokers are almost always retained by the policyholders. Insurance companies may connect policyholders to intermediaries but only become involved when the negotiation and payment processes are largely complete.
The brokers work in close cooperation with the insured’s IT team to assess the best course of action, based on an assessment of costs and benefits to the victim, including the operations and data affected and the extent of any business interruption. While these paid advisors are negotiating with threat actors, additional work is typically undertaken in the background to liaise with law enforcement agencies. The goal is to assess if recoverability from backups is an option and how likely a ransomware gang will return any stolen data.
Ultimately, the victim company will decide how to respond to the extortion. At the same time, the intelligence provided by a ransom negotiator can convince the insured not to pay (for example, if the negotiator has prior experience of the threat actor not releasing effective decryption keys), even if that triggers an insurance payout for the costs of remediation. Indeed, while many insurance policies require the insurer’s consent to pay a ransom, this is not the case when the decision is not to pay a ransom.
Insurance helps improve overall cyber hygiene standards
Apart from helping the insured cope with an attack, insurance can also play an important role in encouraging good cyber hygiene and risk prevention. Through premium discounts, co-insurance and retention arrangements as well as cover limits, insurance can incentivise organisations to adopt essential cybersecurity best practices (for example, investing in state-of-the-art backup systems, endpoint and anti-virus protection, implementing the latest software patches, and security awareness training for all employees).
These all should work to reduce rather than increase the chances of being hit by ransomware attacks.
According to a recent survey by Marsh/Microsoft, the majority of corporate respondents said insurance is an important part of their cyber-risk management strategy, with 41% reporting that insurers’ requirements influenced their decisions to augment existing controls or adopt new ones.
The challenge for re/insurers is keeping track of the highly dynamic cyber risk landscape and adapting the availability and terms and conditions of cover as well as their services to better reflect the threats and vulnerabilities of the insureds.
Early cyber underwriting practices relied heavily on simple questionnaires – often completed only once a year – to assess individual firms’ cybersecurity, which provided basic metrics to support product and price differentiation.
More recently, insurers have introduced more stringent requirements for coverage. Typical examples are multi-factor authentication on remote connections, endpoint detection, privileged access management tools and robust business-continuity planning such as regular backups.
Some re/insurers have also proactively invested in new ways to assess insureds’ cyber maturity and security controls.
These include adoption of new technologies to scan clients’ internal networks to identify policyholders’ potential susceptibility to attack and prompting remedial action that improves a policyholder’s security posture.
Re/insurers have a way to go to in terms of upgrading cyber underwriting to better assess and price the risks (see Cyber Risk hits the top spot in Allianz Risk Barometer). Some studies highlight how the positive effects of cyber insurance to incentivise stronger cybersecurity practices, particularly for small businesses, have yet to materialise fully.
Apart from helping the insured cope with an attack, insurance can also play an important role in encouraging good cyber hygiene and risk prevention.
While insurers can leverage their own claims data, they are often hampered by a lack of reported incidents (especially in unregulated industries and SMEs) and may have limited understanding of the root causes of incidents, cybercriminals’ TTPs, etc.
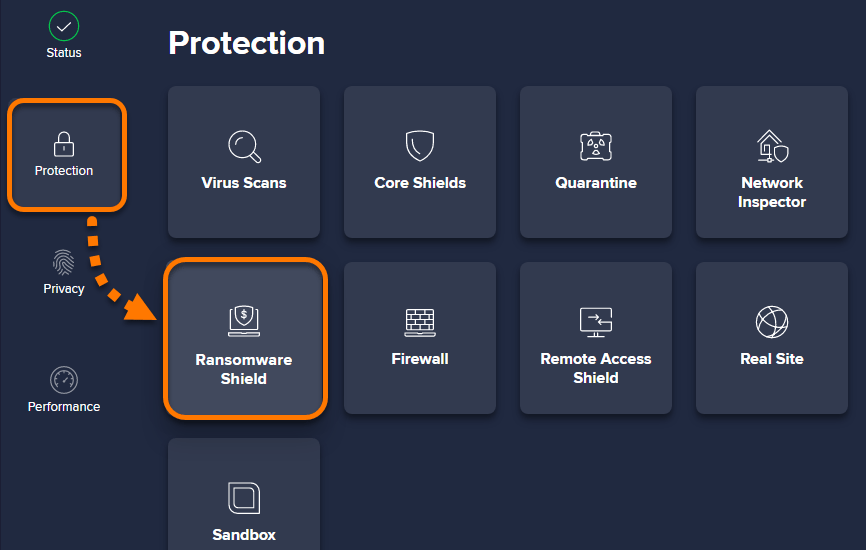
How cyber insurance helps policyholders confront a ransomware attack
Insurers increasingly offer a variety of pre- and post-incident services that help their policyholders prevent, mitigate and respond to cyberattacks. These services augment the traditional loss indemnification role of cyber insurance in supporting ransomware victims, including absorbing the costs of restoring or decrypting data and compensating firms for lost income caused by business interruption/system outage.
Pre-incident guidance
As part of applying for cyber insurance, the underwriting process will often uncover weaknesses in an organisation’s cybersecurity posture and provide guidance for strengthening its cyber resilience.
Some carriers (directly or via partnerships with cybersecurity experts) are also able to monitor continuously observable information about their policyholders’ and applicants’ networks, alerting the insured to vulnerabilities that could also be found by attackers. In many cases, those issues can be addressed quickly, enabling companies to avoid or mitigate an attack.
Many insurers also offer products and services that can assist policyholders in preventing and/or preparing for a ransomware event – for example, employee training and testing, vulnerability scans, incident preparedness exercises, and consultation with legal counsel and loss prevention/security professionals.
Such affiliated services are in fact increasingly demanded as part of cyber insurance solutions. A recent survey revealed that 62% of CEOs believe the provision of network security tools (e.g. firewalls) should be routinely included as part of cyber insurance.
Post-incident support
Cyber insurance policies typically cover the fees charged by external experts (e.g. legal counsel, forensic investigators, ransomware negotiators) who are often brought in to respond to a ransomware attack.
While insurers have established relationships with these specialists and can put the policyholder in touch with the right vendor immediately – very important during a crisis – the vendor will enter into a relationship with the policyholder, making the policyholder their client, not the insurer.
Sometimes it may not be easy to validate whether resilience measures have been appropriately implemented. Enhanced data capture and analysis – especially combining threat/vulnerability intelligence with actual loss experience – is coming on-stream to help identify important predictive (and possibly causal) factors behind particular claims and highlight the best means of risk mitigation.
This will enable more accurate risk-based pricing of cyber insurance and foster stronger incentives for enhanced cybersecurity.
Governments and regulators must go further to counter ransomware attacks
There is no silver bullet for ransomware, and a multi-faceted approach will be required to reduce the underlying drivers, limit their impact and ensure business resilience. Governments along with their regulatory and supervisory agencies have an important role to play in improving the security of cyberspace and helping legitimate businesses gain the upper hand against cyber adversaries.
Many of the suggestions highlighted by re/insurers are mirrored in measures already announced by various governments to enhance cybersecurity in the wake of the recent ransomware epidemic.
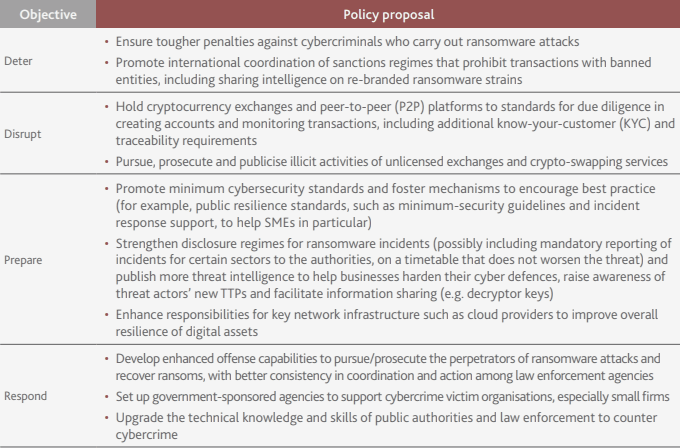
Table presents suggestions from re/insurers for policies aimed at deterring ransomware attacks, disrupting cybercriminals’ business models, preparing organisations better against intrusions and responding to attacks more effectively.
Re/insurer suggestions for possible government policies to counter ransomware
Most obviously, improved mechanisms to track, monitor and share information about ransomware strains should be beneficial. The threat intelligence gathered by government-sponsored security agencies could be used to identify and track down cybercriminals. It could also provide advanced warning as well as guidance to victims on effective counter measures and decryptor tools to contain any spread of the malware.
Recent government-led initiatives to counter ransomware
Rather than ban ransom payments altogether or amend existing sanctions regimes, which may simply create additional complexity, numerous governments instead seem to be coalescing around a combination of enhanced security measures to counter the rise in ransomware.
Enhanced disclosure regimes
A number of countries have set out proposals to strengthen the reporting of ransomware incidents, including the payment of ransoms. Especially noteworthy is the U.S. Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA), which became law in March 2022.
Updating disclosure laws should help increase understanding of the scope and scale of the crime, allow for better estimates of the societal impact of these payments and enable better targeting of disruption activities.
In addition, requiring ransomware victims to report details about the incident prior to paying the ransom enables national governments to take action, for example issuing a freeze letter to cryptocurrency exchanges.
Regulation of cryptocurrencies
Many national authorities now impose restrictions on users and the infrastructure associated with virtual currencies and other crypto assets. In particular, most countries are rolling out tax laws and anti-money laundering (AML)/ combating the financing of terrorism (CFT) laws, or both, to organisations involved with cryptocurrencies, similar to those that apply to banks and other financial services (see our Crypto Market Review).
In November 2021, 103 jurisdictions subjected cryptocurrencies to these laws, with the majority applying both. This compares with the situation in 2018 when 33 jurisdictions regulated cryptocurrencies in these areas, with only five applying both tax and AML/CFT laws.
More effective incident response and international cooperation
Some countries have dedicated ransomware-response platforms, through which businesses and the general public are informed about the latest threats, as well as how to increase their resilience, report ransomware attacks and access a repository of decryption keys for specific types of ransomware.
For example, the ‘fight ransomware’ campaign of the Hong Kong Computer Emergency Response Team Coordination Centre (HKCERT) provides detailed guidance on incident handling.
Similarly, the Cybersecurity & Infrastructure Security Agency (CISA) in the U.S. provides resources, alerts and a reporting tool through a dedicated ransomware platform.
Recognising the global cybersecurity threat posed by ransomware, the recently established U.S.-led Counter Ransomware Initiative aims to enhance cooperation and coordination among the 30 participating countries to boost network resilience, tackle abuse of financial infrastructure for money laundering purposes and foster collaboration among law enforcement agencies.
In a similar vein, INTERPOL has urged a coordinated approach among police forces globally to counter ransomware, akin to their approaches to fight terrorism or disrupt organised crime groups.
Cyber security governance and certification
Beyond regulations and law enforcement, most governments seek to foster enhanced cyber resilience by encouraging cybersecurity best practices. Some authorities are also taking steps to address vulnerabilities in software supply chains. For instance, ENISA, the EU agency for cybersecurity, recently launched cybersecurity certification schemes for IT products, cloud services and 5G networks, enabling users to assess whether products and services meet minimum cybersecurity standards.
EU member states agreed on the Network and Information Security (NIS) 2 Directive, which mandates that a wider scope of critical sectors adopt cybersecurity measures, requires covered firms to assess the cybersecurity of their supply chains and holds executives accountable for cyber breaches.
Some of the cybersecurity vulnerabilities most commonly exploited by cybercriminals to distribute ransomware are years old.
Government intervention could also extend to create increased accountability for software and hardware vendors for intrinsic product failings. The current model of build, sell and patch flaws as they come to light fosters latent zero-day vulnerabilities – software weaknesses that can be exploited by attackers before the developer knows about them – which cybercriminals thrive upon.
Tougher rules against distributing software with weak cybersecurity, potentially with enhanced liability regimes for harm caused by obvious security flaws, could incentivise more stringent testing and remediation of defects. However, authorities need to be mindful not to discourage innovation and increase software/hardware development costs.
Tighter cryptocurrency regulations to help identify and root out illicit transactions, enhanced cryptocurrency tracing, forensics and other blockchain intelligence tools to recover stolen funds will be needed – especially to counter emerging trends such as the adoption of privacy-protecting coins and use of decentralised exchanges that make investigating online crimes and enforcing sanctions difficult (see our research How Industries benefit from Blockchain?).
Together with high-profile public seizures, this will act as a deterrent: if cybercriminals know law enforcement can seize their cryptocurrency, it may lower their incentive to use it in the future.
……………………………
AUTHORS: Darren Pain – Director Cyber and Evolving Liability Geneva Association, Dennis Noordhoek – Director Public Policy & Regulation Geneva Association