Overview
The cyber insurance market continues to evolve and adapt to the changing threat landscape, as cybercriminals and nation states exploit security vulnerabilities and societies’ reliance on digital technology.
A surge in ransomware claims over the past two years, combined with a growing recognition of the threat posed by cyber risks, has caused many insurers to pause and reassess their cyber underwriting strategy.
According to The Geneva Association Report Insuring Hostile Cyber Activity, this has resulted in a reduction in policy limits, a rise in premium rates and a tightening of terms and conditions. It has also triggered a renewed focus on cyber exposure management and deeper consideration for potential future loss scenarios.
The cyber landscape is evolving rapidly
The cyber landscape is evolving rapidly, with digitalisation expanding the range of threats and vulnerabilities. This process is amplified by shifts in working and business practices brought on by COVID-19, some of which are likely to persist beyond the pandemic.
Ransomware and supply chain attacks in particular have become more prolific since the onset of the pandemic and with them wider recognition of the potential for large-scale economic disruption from malicious cyber incidents.
A dedicated market for cyber insurance has developed, involving a progressive broadening in the class of risks covered, both first- and third-party losses.
A dedicated market for cyber insurance has developed over time involving a progressive broadening in the class of risks covered, both first- and third-party losses. However, the recent increase in loss ratios, especially on standalone cyber insurance – i.e. dedicated affirmative cover – has prompted re/insurers to recalibrate cyber risks.
Coupled with initiatives to remove unintentional cyber exposure from conventional property and casualty policies (non-affirmative or ‘silent’ cyber), market re/insurance capacity has become scarcer. In the face of continuing strong demand, this has triggered a sharp rerating in the cost of cyber insurance and a tightening in terms and conditions.
A particular challenge for cyber insurers relates to state-sponsored cyberattacks that may be part of ongoing support for terrorist or criminal groups and stop short of outright military conflict.
Traditional policy exclusions for war or war-like incidents fail to adequately capture situations where nation states are suspected of being behind an attack, or providing a safe harbour for the hackers, especially if the motives for the attack are unclear. Such issues of attribution and characterisation create significant contractual uncertainty for insurers, which has only added to the recent tightening in cyber insurance market conditions.
Accumulated losses of some cyber risks linked to HCA may not be able to be safely and sensibly absorbed by the private re/insurance sector
The size of potential losses from a major HCA or similar incident, relative to the extent of cover currently provided by re/insurers, highlights a significant protection gap.
In order to close at least some of that gap, significant progress is needed in making catastrophic cyber risk more insurable. This would require further improvements in modelling of possible cyber incidents in order to quantify potential losses; advances in sharing cyber threat intelligence and identifying/pursuing perpetrators to deter criminals, terrorist groups and governments who promote HCA and other malicious cyber activity; and having mechanisms for re/insurers to cap their aggregate downside exposures that otherwise would exceed their balance sheet capacity.
Designing such government-backed solutions is complex. There will be trade-offs in adopting particular scheme features and difficulties in calibrating how much of the peak losses should be shared among policyholders, private re/insurers and governments.
Such design challenges are amplified at the international level. Therefore, while collaborative international solutions would be optimal, priority should be given to developing domestic PPP solutions for large-scale cyber risks.
The emerging cyber risk landscape
The ongoing diffusion of new digital technologies into everyday life and business has fundamentally affected the risk landscape facing firms and individuals. Although technological advances create many benefits to improve our lives and lifestyles, they also leave users open to security and associated cyber threats.
Many of the developers of new technologies often tend to focus on the technology itself rather than safeguarding the new technology against basic threats. For example, some smart home devices, whilst easing interconnectivity, may not always include basic cybersecurity hygiene features, leaving them prone to failure and/or attack.
Technological advances can improve our lives and lifestyles but they also leave users open to security and associated cyber threats
More generally, organisations of all sizes, geographies and industries increasingly rely on data analytics and technology, such as cloud computing, the Internet of Things (IoT) and artificial intelligence. In the cyber vernacular, the attack surface/ set of vulnerabilities has grown and the threat vector has expanded, including both accidental, unintentional physical or logical errors and intentional action by malicious attackers. It is the combination of threats and vulnerabilities that gives rise to cyber risks (see our report Cyber Insurance Market Struggles With Ransomware Attacks).
This heightened risk profile poses a challenge to cyber insurers in terms of sustainably increasing the scope and scale of coverage, especially given the potential for large-scale aggregate losses from a cyber incident.
Evolving threats and vulnerabilities
With the increasing digitalisation across nearly all industries, businesses depend more and more on externally managed IT service providers, and many new businesses build their entire business model within a cloud environment.
Notably, only a handful of large companies provide the vast majority of cloud computing capacity, such as Amazon Web Services, Microsoft Azure or the Google Cloud. Market concentration among a few large cloud providers presents a concerning illustration of a potential ‘single point of failure’ in the cyber domain, although thankfully the risk of a massive outage has so far not crystallised.
The response to the global spread of COVID-19 in 2020/2021 has only accelerated prevailing digital trends and amplified cyber risks. Many sectors of the economy saw widespread adoption of internet-based remote working, virtual interactions via video-conferencing and a pronounced expansion of e-commerce.
Ransomware and supply chain attacks in particular have grown considerably in the recent past
Ransomware attacks in particular have grown considerably – by almost 500% from Q1 2018 to Q4 2020 – with no sign of any let up in 2021, significantly outpacing the number of incidents involving data breaches.
This increase in the frequency of attacks has been accompanied by increased sophistication and larger extortion demands, in part linked to the development of ‘ransomware-as-a-service’ (RaaS), whereby specialist malware developers sell software code to other cybercriminals.
According to the U.S. authorities, USD 590 million worth of payments relating to ransomware were made in the first six months of 2021, more than the USD 416 million reported for the whole of 2020.6 Critical infrastructure and operational technology have been prone to ransomware attack – especially those involving RaaS schemes – as aptly illustrated by the recent attack on Colonial Pipeline, which temporarily disrupted the U.S. East Coast’s fuel supply (see Ransomware Attacks & Cyber Insurance).
Software supply chain attacks, i.e. malware introduced via software distributions from legitimate third-party actors, have also received renewed attention, due in large part to the SolarWinds cyberattack revealed in December 20208 and the security breach at Microsoft Server Exchange in early 2021.
Likewise, in February 2021, hackers tampered with a water treatment facility in Florida to change the chemical levels of the water supply, underscoring the vulnerability of industrial infrastructure to such malicious intrusions.
More recently, hackers stole login credentials and addresses of over 1 million customers of web-hosting firm and domain registrar GoDaddy, putting those accounts at high risk of being targeted in future business email scams and phishing campaigns.
While cyber terrorist or other large-scale, malicious attacks causing systemic cyber losses have not been observed so far, it is well documented that criminal gangs are highly active and continuously expand their cyber capabilities, often under the cloak of protection of nation states.
Indeed, nation-state-sponsored hackers are believed to be behind the recent SolarWinds and Microsoft attacks, not least because of the high level of sophistication and long planning horizons involved.
Cyber warfare is increasingly regarded as part of a nation’s arsenal alongside traditional military force, with correspondingly large resources deployed. Yet so far these state-sponsored cyber incidents have been covert, rather than overt operations. As such, they are part of what is currently best described as a ‘cold cyber war’ rather than necessarily a prelude to a full-scale kinetic war.
The cyber insurance market
The market for standalone cyber insurance, i.e. dedicated affirmative cover, has grown rapidly over recent years, with premiums more than tripling since 2015 to reach around USD 7.5 billion in 2020.
Although that still represents a relatively small share of global expenditure on insurance, over time, the breadth of cover has developed to include a wider set of protected assets, both tangible and intangible.
Vastly expanded data privacy legislation both in Europe (the EU General Data Protection Regulation, or GDPR) and the U.S. (most notably the California Consumer Privacy Act, or CCPA) have led to further recent expansions in coverage. Nowadays, affirmative cyber insurance typically extends protection to incidents beyond computer security failures and data breaches and combines coverage for a wide range of first-party as well as third-party losses – albeit often with specific and relatively modest policy limits.
Affirmative cyber insurance extends protection to a wide range of first-party and third-party losses – albeit often with specific and relatively modest policy limits
However, a number of key risks are not covered within affirmative cyber policies, e.g. bodily injury, property damage and losses arising from the failure of critical infrastructure.
Over the past few years, the insurance industry has strived to minimise exposure to ‘silent’ cyber given the unintended nature of coverage. In part, this effort is in response to regulatory initiatives14 that require insurers to explicitly either include or exclude cyber coverage from their regular property and casualty policies.
Insurers need to know their exposures and hence be able to calibrate their cyber risk across the full suite of insurance policies and have sufficient solvency capital to guard against possible large loss accumulation events. Equally, the policyholder gains increased contract certainty about cyber risks that are covered and those that are not Some insurers have clarified coverage by defining cyber risk and then excluding it from non-cyber policies.
Some are introducing new policy language and underwriting guidelines. Others, such as Lloyd’s of London, require insurers to either expressly exclude or include cyber risk in their traditional lines’ policy wordings.
Recent withdrawal of risk-absorbing capacity
Amid heightened uncertainty about prospective cyberattacks, especially the potential for ransomware and supply chain incidents to have widespread impacts, re/insurers have recently sought to tighten policy language and withdraw risk-absorbing capacity in order to protect their balance sheets.
Measures include coverage exclusions, higher self-insured retentions and more stringent limits/sublimits. This restriction in market capacity, alongside ongoing demand, is showing up in significant increases in the price of affirmative cyber cover as the overall cost of protection has been recalibrated.
Re/insurers have recently sought to tighten policy language and withdraw risk-absorbing capacity, prompting a sharp increase in premium rates.
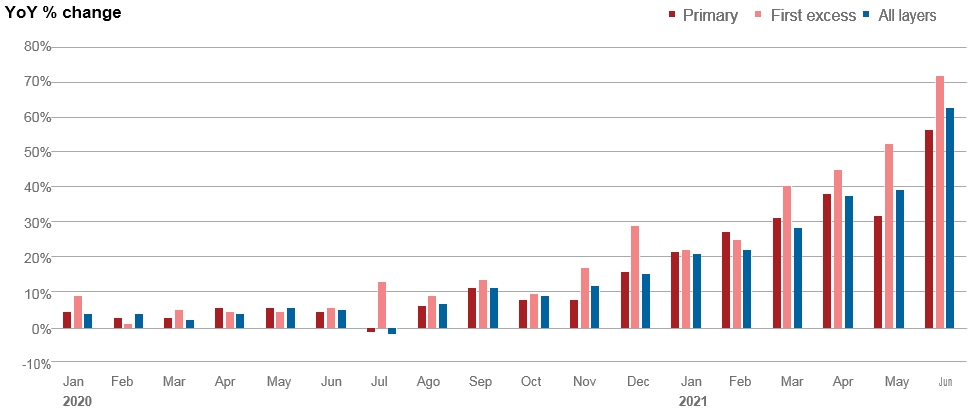
Year-on-year cyber premium rate increases averaged around 15% between January 2020 and June 2021. However, this masks a more significant hardening in the market in late 2020 and the first half of 2021. For cover involving higher policy limits (i.e. excess-of-loss cover) the recent pick-up in rates was even larger, perhaps consistent with increased worries about the frequency and severity of possible large-scale attacks, which could burn through the primary layer protection.
That upward pricing momentum continued through the remainder of 2021 with rates on affirmative cyber policies increasing in the year to Q3 by 96% in the U.S. and 73% in the U.K., driven by a rise in the frequency and severity of losses.
Cyber insurance premium rate increases over the course of contract renewals, by layer of cover
Hostile cyber activity
Recent serious supply chain intrusions and ransomware incidents have underscored a long-standing issue for cyber insurers: how much protection can and should insurance provide when the perpetrators of such attacks are linked to nation states?
Traditional policy exclusions for war or war-like incidents fail to adequately capture situations where nation states are suspected of being behind an attack or at least providing a safe harbour for the hackers, especially if the motives for the attack are unclear. Such issues of attribution and characterisation create significant contractual uncertainty for insurers, which has only added recently to the tightening in cyber insurance market conditions.
Traditional war exclusions fail to adequately capture situations where nation states may be behind an attack, creating contractual uncertainty
Initiatives to tighten cyber policy language and introduce more granular terminology for insured events will no doubt help.
The Lloyd’s Market Association issued new cyber war and cyber operation exclusion clauses which seek to articulate the coverage position more clearly in the context of cyber warfare. However, it takes time for such changes in wordings to gain market-wide support let alone be introduced into standard commercial insurance products.
Moreover, the latest incidents also highlight the residual challenges in creating clear-cut, definitive boundaries around what legitimately falls within HCA and what does not. Rather than the pursuit of political aims, which is normally a defining feature of terrorist activity or warfare, many of the recent attacks were carried out by organised criminal gangs principally for financial gain.
Nation-state involvement also varied widely, from reported tacit sponsorship, including fostering an environment for developing sophisticated yet easy -to-use malware (e.g. the attack on Colonial Pipeline), to alleged outright supervision and resourcing of hacking campaigns by official arms of a sovereign government (e.g. SolarWinds). In such circumstances, some of the difficulties of direct attribution for HCA resurface, particularly if state actors linked to criminal gangs use false-flag tactics to hide their traces, blame others or otherwise undermine any international consensus about the ultimate source of the attack.
However, attribution challenges can resurface if state actors linked to criminal gangs use false-flag tactics to hide their traces, blame others or undermine international consensus about the source of the attack.
On the other hand, the systemic characteristic of such cyber risks and in particular the potential for multiple losses from a single incident or a campaign of attacks mean that the scale of accumulated losses may exceed levels that can safely and sensibly be absorbed by the private re/insurance sector. There is often collateral damage surrounding any large-scale malicious cyberattack whereby unintended targets also suffer loss.
Ultimately, individual insurers will decide how they balance the commercial attractions of growing their cyber insurance portfolios versus their risk appetite and capacity for absorbing possible peak losses (see Cyber Insurer Perspectives on Ransomware. Insurance Market Outlook).
There is to date, and unlikely to be in the near future, no universal consensus within the re/insurance market regarding how HCA should be included or excluded for various cyber insurance policies. Some carriers may continue to cover HCA but carefully limit their exposure in a bid to prevent potential loss accumulation. Others will shy away from cyber exposure altogether, fearful of the fallout from further escalation in HCA.
The cyber insurance market tends to be concentrated, with relatively few insurers targeting this specialty line. A key factor in encouraging both incumbent and prospective insurers to offer increased coverage for HCA and other malicious cyber activity will be advances in modelling and the quantification of cyber risks, as well as reinsurance availability and other mechanisms to share risks.
Quantifying HCA risks
Unlike for natural catastrophe perils such as hurricanes or man-made disasters such as terrorist attacks, cyber as a peril has no geographical borders – the whole world is potentially one cyber catastrophe zone. Beyond issues of attribution and characterisation, assessing the frequency and severity of HCA, especially the potential for large accumulated losses, remains a particularly serious challenge.
Realistic disaster scenarios
Scenario analysis can help to gauge the potential for losses from HCA, especially complex accumulation. In particular, different configurations of attack (threat source, points of vulnerability, propagation and correlation of attack, etc.) can inform about the scale of potential damages and the economic losses at stake.
Catastrophe model vendors and insurers or large re/insurance markets like Lloyd’s have articulated cyber catastrophe scenarios (often labelled realistic disaster scenarios) in order to understand the potential financial implications. Typically deterministic, such hypothetical scenarios seek to provide ‘what-if’ type guesstimates of the impact should downside risks crystallise. By careful selection, construction and analyses of different scenarios, a broad picture of the size of possible losses can be created.
Existing cyber risk scenario analysis
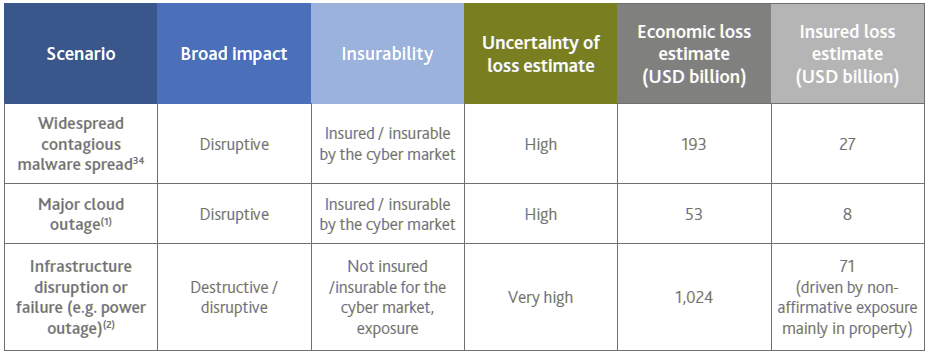
At face value, projected total economic losses from either a widespread malware attack and/or major cloud outage, while significant, are not unprecedented.The direct estimated costs are broadly comparable with those previously experienced from a large natural catastrophe – for example, in U.S. communities affected by major hurricanes, the U.S. National Oceanic and Atmospheric Administration’s (inflation-adjusted) estimates of economic damage were USD 176 billion for Katrina, USD 77 billion for Sandy, USD 136 billion for Harvey and USD 55 billion for Irma.
Projected economic losses from a widespread malware attack and/or major cloud outage, while significant, are not unprecedented
More than for these natural catastrophes, however, the projected share of extreme cyber losses that would be insured – based on current coverages – is relatively small. Assuming that re/insurers can better understand the likelihood of such events, as well as control potential loss accumulation through analysis of the maximum footprint or ‘spread’ of impacts from such an event, in principle insurance can play a bigger role in closing the protection gap for such risks.
Uncertainty surrounding loss quantification
The level of uncertainty surrounding such extreme loss scenario estimates is nevertheless very high. In terms of loss accumulation, it is extremely challenging to identify the full set of dependencies among risks, define scenario footprints and assess the impact of an event on the many companies that could be affected. The frequency and severity of cyber events as well as their co-dependence are not easy to establish, making it difficult to assess potential overall aggregate losses.
The potential for ‘unknown-unknown’ cyber threats creates significant ambiguity about the underlying sources and size of exposure.
Cyber risks are highly interdependent, meaning that losses can often accumulate significantly, especially if any correlating cause takes time to reveal itself.
Counterfactual simulation analysis (looking at actual events and projecting just how bad they might have been) can help. But determining the potential scale of such an event requires a large element of judgment.
Obstacles to modelling and quantifying HCA risks
Scenario-based accumulation risk modelling works well within the normal ‘cold war’ state of affairs, but it has significant shortcomings at times of heightened potential for rapid intensification of nation-state cyber tactics.
As hostile situations escalate from a ‘stable’ level of isolated, covert offensive HCA to more brazen infiltration campaigns, and even possibly a state of full out ‘cyber war’, model assumptions around the frequency of a one-off systemic attack may no longer be realistic. For instance, it is imaginable that successive massive retaliatory attacks take place over a short period of time, each of magnitude in line with say a 1-in-100-year event under ‘non-war’ conditions.
The likelihood or severity of losses are unclear if there is an escalation of cyber war-like incidents and the contours of the tail of the aggregate loss probability distribution are highly imprecise.
If insurers cannot rule out the possibility of an ongoing overt conflict, then they need to allow for this in their risk evaluations. However, given the human behavioural aspects involved, it is difficult to assess any retaliatory action and/or the potential for similar or worse attacks to be used as war-like responses to states that are attacked. It is also not known what the potential likelihood or severity would be if there is an escalation of cyber war-like incidents. As a result, the contours of the tail of the aggregate loss probability distribution are highly imprecise.
The formal assessment of cyber risk in all its features is still in its infancy, and more needs to be done, in particular in the area of systemic risk.
Alternative risk transfer options
Insurance typically involves a delicate balance between supply and demand. Re/insurers need to set coverage conditions and charge sufficient premiums to cover the costs of providing risk protection, including compensating the providers of their capital for potential unexpected losses.
Risks are only insurable in practice if an insurer and an insurance buyer reach an agreement about a specific coverage and its price, including a common understanding of what is insured and what is not.
At the same time, there needs to be demand for such cover on those terms. For this reason insurance can only deal with a limited band of the full spectrum of risk.
Boundaries between insurable and uninsurable risk
In order to understand the potential appetite of the insurance industry to absorb HCA risks, it is worthwhile to briefly review cyber risks against key actuarial criteria for insurability.
In particular, the ability to insure cyber risk will often turn on insurers’ assessment of how far
- (a) the probability of loss is random and can be estimated
- (b) the presence of insurance influences the probability of loss (i.e. moral hazard)
- (c) the loss accumulation potential is economically bearable
Governments could control the frequency of cyberattacks and the presence of insurance might influence their willingness to engage in hostile activities.
Moreover, cyber losses are not the outcomes of a game against nature in the way that, for example, air and ocean surface temperatures create conditions for weather storms. Governments could theoretically control the frequency of attacks at will, and the presence of insurance to cover collateral damage of their own industries might influence their willingness to engage in hostile activities.
They could be more likely to launch attacks – or to take other aggressive actions that invite retaliation in cyberspace – if any cyber repercussions are mitigated by insurance payouts. This potential for government moral hazard contrasts with the situation often facing individuals and firms.
However, insurers must not only assess the risk of an individual or company becoming the victim of a cyberattack but also the scope for multiple insureds to be impacted. HCA has the potential to create catastrophic, highly-correlated, unpredictable losses, which insurance contracts were not intended to cover. If the insurance industry were to proactively broaden cover to HCAs, this additional dimension of accumulation risk would seriously need to be addressed.
Enlarging market capacity for insurable risks
In some countries, commercial insurance offerings for cyber terrorism may be available under one of the existing terrorism pools, particularly where it results in physical property damage. But policy limits are still, in general, quite low.
A captive can be a useful way for a company to recognise and gain a better understanding of its cyber exposures. By building up a track record of its losses and expenses as well as its risk mitigation efforts, the captive may be able to secure coverage from the re/insurance market at acceptable terms and pricing.
This may particularly be the case when a re/insurer agrees to share certain risks with the captive. For example, a re/insurance carrier may not wish to underwrite the primary layer of losses for certain risks (or industry sectors) but might provide excess-of-loss cover.
Captives are not alone in preferring discrete risks with clear boundaries. Traditionally, pools have operated for distinct risks within a strictly confined geographical boundary. Most pools are designed to diversify independent risks, or at least shocks that might not hit all of the members of the pool simultaneously.
However, such mutualisation of possible losses breaks down when a common event affects all insureds, with the potential for losses to exhaust any buffer funds accumulated by members of the pool.
According to ILS Market Cyber Insurance Survey to date the market for ILS – financial instruments sold to investors and whose value is affected by an insured loss event – has developed substantially within the property catastrophe arena. This is largely due to the perceived positive risk/reward balance in peak natural catastrophe perils and the availability of third-party analytic tools. However, natural catastrophe claims over the last three years have seen ILS investors suffer disproportionately large losses from the concentrations in major peak weather catastrophe zones.
As a result, some ILS managers and investors are reportedly seeking portfolio diversification by assuming exposure to other insured perils and reducing, in particular, their exposure to U.S. East-Coast wind events.
For years, the global reinsurance industry have either lamented the inability to access insurance linked securities’ (ILS) capacity for cyber risks or simply declared that ILS should become available to help with no reason other than the traditional market’s need for capital.
As a result, it appears that a mix of frustration and disinformation swirled across the global re/insurance industry regarding the ILS market, its appetite for cyber risk, and the barriers between Cyber Insurance Linked Securities and the cyber re/insurance market.
Some commentators argue that peak cyber risks will eventually be securitised and transferred to capital markets, especially as any such instruments would likely attract high yields.
So far, however, such initiatives remain largely theoretical with few, if any, transactions, at least in the public domain. Similar to pandemic risk, the potential for a large-scale cyber incident to simultaneously hit stock and bond market valuations, thereby undermining any diversification benefits, remains a significant hurdle for third-party investors.
Public-sector solutions to catalyse future market development
Re/insurers are only likely to be able to take on more HCA risk if there is a way of capping overall aggregate losses. Echoing current debates over pandemic-related risks, consideration should thus be given to government-backed solutions to finance these tail cyber risks in order to boost economy-wide resilience.
A well-designed PPP could increase risk-absorbing capacity and still encourage cyber market innovations to extend cover further for HCA risks. This is evident in long-standing PPPs for terrorism and other perils.
In developing and establishing a PPP in any jurisdiction a key challenge is how to divide the risk between the public and private sectors.
To incentivise good cybersecurity, as much risk as possible should remain with firms and individuals and be underwritten by private insurers on commercial terms with public-sector involvement limited to extreme loss outcomes. Any government-backed solutions should not simply be a fiscal solution but also seek with insurers to promote adoption of cybersecurity best practices – including taking out appropriate insurance – in order to reduce the vulnerability of society to such risks.
Designing a government-backed insurance solution
There are many and varied ways in which a government-backed solution for peak cyber risks could be formulated. The main ones are as a direct insurer operated by or alongside the government, a state-run reinsurance facility to protect against large-scale, catastrophic losses or a private-sector pool with a government (retrocession) backstop.
The criteria for developing a framework upon which a government may either support or be involved in providing insurance solutions revolves around a number of important design questions:
- Should the insurance exist solely for HCA and cyber terrorism perils or as a subset of broader cyber risks? Alternatively, should it be part of a multi-peril solution? Could there be an umbrella pooling scheme in place?
- Should any proposed solution be compulsory or voluntary?
- Should the scheme be pre- or post-funded? What mechanisms may be used to determine factors affecting the capital raising and financial sustainability of the scheme?
- What is the event and claims assessment basis – indemnity or parametric?
- Should any scheme be based on mutuality or solidarity principles?
- Will it be a permanent or temporary scheme?
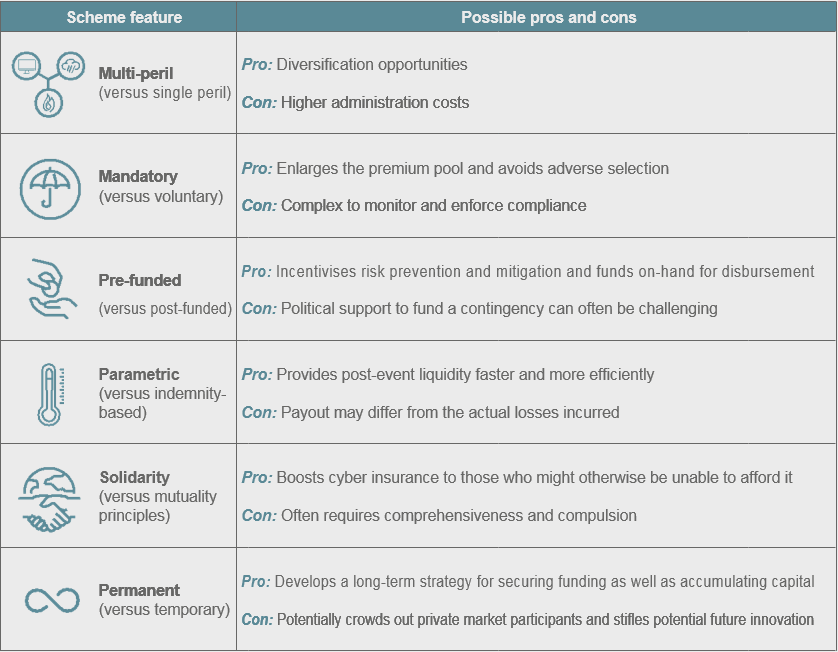
Taken together, the answers to these questions ought to help shape any government involvement as well as how any PPP could be designed. There are likely trade-offs in adopting particular scheme features and empirical difficulties in calibrating how much of the tail losses should be shared among policyholders, private re/insurers and governments.
These trade-offs may vary between jurisdictions and be guided by different commercial realities, economic considerations and political influences. It is unlikely that any single factor will determine the outcome. There may also be scope to continue to adapt and re-optimise the solution, including in response to the evolving nature of the risk and the available capacity of the commercial insurance market to absorb cyber risks.
While a multi-peril scheme may offer some diversification benefits, it also increases the chance of reliance on any government backstop.
Mandatory insurance enlarges the potential premium pool but raises the question of how to enforce the scheme and what (if any) sanctions will apply for those not taking out coverage.
Risk is spread over a larger base and adverse selection is reduced. But it also raises the question of how to enforce the mandatory aspects of the scheme and what (if any) sanctions will apply for those not taking out coverage. The administration efforts to ensure those required to obtain cover do so and pay the required price may create significant operational costs.
One way in which mandatory take-up could be assured is to administer this in conjunction with business taxation or as a requirement for the operation or continued operation of a business.
A pre-event-funded scheme can build in features to incentivise risk prevention and mitigation
Governments tend to favour post-funding arrangements as garnering political support to fund a contingency that may never arise can be challenging. Post-funding may also be attractive because it avoids having to set up a potentially large bureaucracy to collect and invest premiums.
Parametric insurance can provide post-event liquidity much faster and more efficiently than traditional indemnity products, but such covers might lead to significant accumulated losses.
To date there has been little commercial appetite to develop parametric insurance for cyber risks. This is most likely due to the potential for parametric triggers to create significant accumulated losses – depending on the scope and breadth of an attack multiple insureds could be impacted, especially if it is part of a sophisticated hacking campaign.
Commercial insurance is based on the premise that risks should be priced in an actuarially fair manner and designed to incentivise the insured to protect themselves against particular contingencies.
If the insurance is set up with mutuality in mind, cover for individual insureds is priced to reflect their contribution to the risk of the overall pool. In contrast, under solidarity principles, there is often a degree of cross-subsidisation whereby some insureds pay higher than actuarially-fair prices in order to subsidise other insureds within the pool.
Permanent PPPs could help with long-term funding strategy development and capital accumulation, but policymakers are cautious that perpetual schemes could crowd out private market participants.
Summary of the pros/cons of possible features of a PPP scheme
This report finalises The Geneva Association’s and IFTRIP’s research trilogy into cyber terrorism, HCA and cyber warfare risks, which brings together insights into the insurance industry’s approach to the insurability of these risks. In particular it builds on the framework developed by The Geneva Association and IFTRIP to define the term HCA.
HCA refers to malicious cyberattacks that extend beyond cyber terrorism but are not cyber war and involve or can be connected in some way to a state actor.
It provides terminological clarity over what in many cases would otherwise be a potential grey area in terms of coverage of events. It assists with the process of attribution and characterisation by lowering the burden associated with having to ‘prove’ which state was responsible for an event.
Such events, which involve state actors but are akin to a cold-war-type event, are at present insured up to certain limits by the private re/insurance sector. Further growth of the commercial cyber insurance market should be encouraged. However, the potential accumulation losses caused by cyber terrorism or HCA events are too big and uncertain for the re/insurance market to absorb alone. As a result, it may ultimately be necessary to develop a PPP solution whereby the public sector absorbs some of the peak cyber risks. Suitably designed, such a PPP could continue to promote expansion and innovation in the private cyber insurance market and ensure fiscal stability to cope with large-scale events.
…………………………
AUTHORS: Rachel Anne Carter – Managing Director Carter Insurance Innovations, Darren Pain – Director Cyber and Evolving Liability The Geneva Association, Julian Enoizi – CEO Pool Re & Secretary International Forum of Terrorism Risk (Re)Insurance Pools